Professional Documents
Culture Documents
PX C 3880642
Uploaded by
Jaka PermanaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
PX C 3880642
Uploaded by
Jaka PermanaCopyright:
Available Formats
International Journal of Computer Applications (0975 8887)
Volume 49 No.3, July 2012
20
Total Edge Irregularity Strength of Butterfly Networks
Indra Rajasingh
Department of Mathematics
Loyola College
Chennai
Bharati Rajan
Department of Mathematics au
Loyola College
Chennai
S.Teresa Arockiamary
Department of Mathematics
Stella Maris College
Chennai
ABSTRACT
Given a graph G (V, E) a labeling c: VE{1, 2 k} is
called an edge irregular total k-labeling if for every pair of
distinct edges uv and xy, c(u) + c(uv) + c(v) = c(x) + c(xy) +
c(y). The minimum k for which G has an edge irregular total
k-labeling is called the total edge irregularity strength of G. In
this paper we examine the butterfly network which is a well
known interconnection network, and obtain its total edge
irregularity strength.
Keywords
Irregular Total Labeling, Interconnection Networks, Butterfly
Networks , Labeling, Irregularity strength.
1. INTRODUCTION
Labeled graphs are becoming an increasingly useful family of
Mathematical Models for a wide range of applications.While
the qualitative labelings of graph elements have inspired
research in diverse fields of human enquiry such as conflict
resolution in social psychology, electrical circuit theory and
energy crisis, these labelings have led to quite intricate fields
of application such as coding theory problems, including the
design of good radar location codes, synch-set codes; missile
guidance codes and convolution codes with optimal
autocorrelation properties. Labeled graphs have also been
applied in determining ambiguities in X-Ray crystallographic
analysis, to design communication network addressing
systems, in determining optimal circuit layouts, radio-
Astronomy, etc.
Interconnection network is a scheme that connects the units
of a multiprocessing system. It plays a central role in
determining the overall performance of a multicomputer
system. An interconnection network is modeled as a graph in
which vertices represent the processing elements and edges
represent the communication channel between them.
Interconnection networks play an important role for the
architecture of parallel computers and PC-Clusters or
Networks of Workstations. Much of the early work on
interconnection networks was motivated by the needs of the
communications industry, particularly in the context of
telephone switching. With the growth of the computer
industry, applications for interconnection networks within
computing machines began to become apparent. Amongst the
first of these was the sorting of sequences of numbers, but as
interest in parallel processing grew, a large number of
networks were proposed for processor to memory and
processor to processor interconnection.
For a graph G (V, E), Baca et al.[1] define a labeling c: V
E {1, 2 k} to be an edge irregular k-labeling of the
graph G if c(u) + c(uv) + c(v) = c(x) + c(xy) + c(y) for every
pair of distinct edges uv and xy. The minimum k for which the
graph G has an edge irregular total k-labeling is called the
total edge irregularity strength of the graph G, and is denoted
by tes(G). More complete results on irregular total labelings
can be seen in the survey paper by Gallian [4] In this paper
we determine the total edge irregularity strength of butterfly
networks. As our main result we prove that the bound on tes
for butterfly networks is sharp.
Theorem 1[1] Let G be a graph with m edges. Then tes(G)
2
3
m+ (
(
(
.
Theorem 2[1] Let G be a graph with maximum degree .
Then tes(G)
1
2
A+ (
(
(
.
Theorem 3[2] A graph G(V, E) of order n, size m, and
maximum degree
n
m
8
10
0
3
< A <
satisfies tes(G) =
2
3
m+ (
(
(
Theorem 4[2] Every graph G(V, E) of order n, minimum
degree > 0, and maximum degree such that
2 4
10
3
n
<
A
o
satisfies tes(G) =
(
(
(
+
3
2 m
.
Theorem 5[2] For every integer 1, there is some n() such
that every graph G(V, E) without isolated vertices with order
n n(), size m, and maximum degree at most satisfies
tes(G) =
(
(
(
+
3
2 m
.
Conjecture (Ivanco and Jendrol[5]) For every graph G with
size m and maximum degree that is different from K
5
, the
total edge irregularity strength equals
max
+2
3
,
+1
2
.
For K
5
, the maximum of the lower bounds is 4 while tes(K
5
) =
5.
Conjecture has been verified for trees by Ivanco and
Jendrol[5] and for complete graphs and complete bipartite
graphs by Jendrolet al. in [6]. As our main result, we prove
the Conjecture for large graphs whose maximum degree is not
too large in terms of the order and the size. We now consider
the butterfly networks BF(r), and prove that for these
networks the bound on tes given in Theorem1 is sharp.
International Journal of Computer Applications (0975 8887)
Volume 49 No.3, July 2012
21
[00,2]
[00,1] [01,1]
[01,2]
[10,2]
[11,2]
[10,1]
[11,1]
[10,0] [00,1] [01,0] [11,0]
mirror image of [01,2]
(a) Normal form
(b) Diamond form
Level 0 Level 1 Level 2
[00,0] [00,1] [00,2]
[01,0] [01,1] [01,2]
[10,0]
[10,1] [10,2]
[11,0] [11,1]
[11,2]
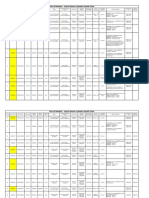
Fig 1: Binary labeling of a 2-dimensional butterfly
2. THE BUTTERFLY NETWORK
2.1 Definition The set of nodes V of an r-dimensional Butterfly
BF(r) corresponds to the set of pairs [w,i], where i is the
dimension or level of a node ( 0 i r) and w is an r-bit binary
number that denotes the row of the node. Two nodes [w, i ] and
[w
, i
] are linked by an edge if and only if i
= i +1 and either
i) w and w
are identical, or
ii) w and w
differ in precisely the i
th
bit.
The r- dimensional butterfly BF(r) has (r + 1) 2
r
nodes and r2
r+1
edges.
Efficient representation for Butterfly and Benes networks
have been obtained by Manuel et al.[9]. The Butterfly in Figure
1(a) is drawn in normal representation; an alternative
representation, called the diamond representation, is given in
Figure 1(b). By a diamond we mean a cycle of length 4. Two
nodes [w, i] and [w
, i] are said to be mirror images of each other
if w and w
differ precisely in the first bit. The removal of level 0
vertices
1
,
2
, ,
2
of BF(r) gives two subgraphs H
1
and H
2
of
BF(r), each isomorphic to BF(r - 1). Since
1
,
2
, ,
2
is a
vertex cut of BF(r), the vertices are called binding vertices of
BF(r).
A 4-cycle xv
1
yv
2
x in BF(r) where (
1
), (
2
) and v
1
,
v
2
are binding vertices of BF(r) is called a binding diamond. The
edges of the binding diamond are called binding edges. For
convenience, we call the edges (x, v
i
) as upper binding edges and
edges (y, v
i
) as lower binding edges. There are exactly two
binding vertices of BF(r) adjacent to a binding vertex of BF(r -
1). One is called the left binding vertex and the other is called the
right binding vertex. See Figure 2.
Butterfly network is an important and well known topological
structure of interconnection networks. It is a bounded-degree
derivative of the hypercube which aims at overcoming some
drawbacks of hypercube. It is used to perform a method to
illustrate FFT( Fast Fourier Transform), which is intensively
used in the field of signal processing.
2.2 Results
2.2.1 Lemma 1: tes(BF(3)) = 17.
Proof: The labeling of BF(3) is shown in Figure 3 and can be
checked manually.
2.2.2 Lemma 2: tes(BF(r)) =
+
+
, r 4.
Input : r- dimensional butterfly, BF(r), r 4.
Algorithm:
1. Label the vertices and edges of BF(3) as shown in Figure 3.
x
y
) 1 (
1
BF H ~
) 1 (
2
BF H ~
1
v
2
v
3
v
4
v
Binding
diamond
Binding
vertexof
BF(2)
Binding
edge
Binding vertex
of BF(1)
Left binding
vertexof BF(2)
Right binding
vertexof BF(2)
Upper binding
edge
Lower binding
edge
Fig 2: Binding vertices and binding edges of BF(2)
International Journal of Computer Applications (0975 8887)
Volume 49 No.3, July 2012
22
1
1
2
2
1
2
2 1
5 5
5
6
6 6
5
6
3 4
3 4
4
4 4 4
2 3
2 3
4 5 6 7 8 9 10 11
11 11 11 11 11 11 11 11
1 2 3 4 5 6 7 8
12
11 11
12 12 13
12 13
13 14
13 14
12 13
12 13
15 15 15 15
16
17
16 17
15 15
16 16
Fig 3:Edge irregular k-labeling of BF(3) when k =17
2. Label the vertices and edges of BF(r ), r 4, inductively as
follows:
Having labeled the vertices and edges of
1
(
1)
(i) Label the vertices and edges of
2
( 1) by
adding =
2
+1
+2
3
(1)2
+2
3
to the vertex labels and s =
t - 1 to the edge labels of
1
.
(ii) Label the binding vertices of BF(r ) from left to right
as 't'.
(iii) Label the upper binding edges from left to right as x,
x+1,x+2,,x+(2
r
-1),where = 3
12
+2
3
+
22
1
+2
3
2
+1
+2
3
.
(iv) Label the lower binding edges from left to right as y,
y+1,y+2,,y+(2
r
-1),where = 2
2
2
+1
+2
3
+
4
(1)2
+2
3
+
(2)2
+1
+2
3
.
Output: =
2
+1
+2
3
.
Proof of correctness.
We prove the result by induction on r. By actual verification, it
is easy to check that the labels given in Figure 3 yield
3 = 17. This proves the result when r = 3. Assume
the result for BF(r - 1). Consider BF(r). Since the labeling of
1
( 1) is an edge irregular k- labeling, it is clear that
the labeling of H
2
obtained by adding a constant to each label
of H
1
using 2(i) is also an edge irregular k- labeling. Since the
labels are consecutive, the sums of BF(r) are also consecutive
integers which are clearly distinct.
From Lemma 1 and 2, we obtain the following result.
2.2.2 Theorem 6: Let BF(r) be a r-dimensional
butterfly network.Then tes(BF(r)) =
2
+1
+2
3
, r 3.
3. CONCLUSION
In this paper, we have proved that Butterfly Networks are total
edge irregular and we have also obtained the total edge
irregularity strength of Butterfly Networks. This problem is
under investigation for certain other architectures like Benes,
Honeycomb and Grid networks.
4. REFERENCES
[1] M.Baca, S.Jendrol, M.Miller, and J.Ryan, On irregular
total labelings, Discrete Math 307(2007), 1378- 1388.
[2] S.Brandt, J.Miskuf, and D. Rautenbach, On a conjecture
about edge irregular total labelings, J.Graph Theory, 57
(2008), 333-343.
[3] G.Chartrand, M.Jacobson, J.Lehel, O.Oellermann,
S.Ruiz, and F.Saba, Irregular networks, Congr.
Numer., 64(1988) 187-192.
[4] J.A.Gallian, A Dynamic survey of graph labeling, The
Electronic journal of Combinatorics 15(2011), #DS6.
[5] J.Ivanco and S.Jendrol, Total edge irregularity
strength of trees, Discuss Math Graph Theory 26(2006),
449-456.
[6] S. Jendrol, J. Missuf, and R. Sotak, Total edge
irregularity strength of complete graphs and complete
bipartite graphs, Elec. Notes Discr. Math., 28(2007), 281-
285.
[7] unming Xu, Topological Structure and Analysis of
Interconnection Networks China, (2001).
[8] X. Liu and Q. P. Gu: Multicasts on WDM All- Optical
butterfly Networks: Journal of Information Science and
Engineering, 18(2002), 1049-1058.
[9] P.Manuel, M.I.Abd-El-Barr, I.Rajasingh and B.Rajan:An
Efficient Representation of Benes Networks
itsapplications: Proc. Of the sixteenth Australasian
Workshop on combinatorial algorithms,
Ballarat,Australia, (2005), 217-230.
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Merchandising Calender: By: Harsha Siddham Sanghamitra Kalita Sayantani SahaDocument29 pagesMerchandising Calender: By: Harsha Siddham Sanghamitra Kalita Sayantani SahaSanghamitra KalitaNo ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Trading As A BusinessDocument169 pagesTrading As A Businesspetefader100% (1)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- CMC Ready ReckonerxlsxDocument3 pagesCMC Ready ReckonerxlsxShalaniNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- 08 Sepam - Understand Sepam Control LogicDocument20 pages08 Sepam - Understand Sepam Control LogicThức Võ100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Archlinux 之 之 之 之 Lmap 攻 略 ( 攻 略 ( 攻 略 ( 攻 略 ( 1 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 )Document16 pagesArchlinux 之 之 之 之 Lmap 攻 略 ( 攻 略 ( 攻 略 ( 攻 略 ( 1 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 )Goh Ka WeeNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Portfolio Artifact Entry Form - Ostp Standard 3Document1 pagePortfolio Artifact Entry Form - Ostp Standard 3api-253007574No ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- MBO, Management by Objectives, Pooja Godiyal, Assistant ProfessorDocument20 pagesMBO, Management by Objectives, Pooja Godiyal, Assistant ProfessorPooja GodiyalNo ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- GlastonburyDocument4 pagesGlastonburyfatimazahrarahmani02No ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- New Education Policy 2019Document55 pagesNew Education Policy 2019Aakarshanam VenturesNo ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- August 03 2017 Recalls Mls (Ascpi)Document6 pagesAugust 03 2017 Recalls Mls (Ascpi)Joanna Carel Lopez100% (3)
- Difference Between Text and Discourse: The Agent FactorDocument4 pagesDifference Between Text and Discourse: The Agent FactorBenjamin Paner100% (1)
- FX15Document32 pagesFX15Jeferson MarceloNo ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Theory of Linear Programming: Standard Form and HistoryDocument42 pagesTheory of Linear Programming: Standard Form and HistoryJayakumarNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Modified Syllabus of Control SystemDocument2 pagesModified Syllabus of Control SystemDigambar PatilNo ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Ultimate Advanced Family PDFDocument39 pagesThe Ultimate Advanced Family PDFWandersonNo ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Wi FiDocument22 pagesWi FiDaljeet Singh MottonNo ratings yet
- S5-42 DatasheetDocument2 pagesS5-42 Datasheetchillin_in_bots100% (1)
- Briana SmithDocument3 pagesBriana SmithAbdul Rafay Ali KhanNo ratings yet
- Decision Maths 1 AlgorithmsDocument7 pagesDecision Maths 1 AlgorithmsNurul HafiqahNo ratings yet
- #### # ## E232 0010 Qba - 0Document9 pages#### # ## E232 0010 Qba - 0MARCONo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- FSRH Ukmec Summary September 2019Document11 pagesFSRH Ukmec Summary September 2019Kiran JayaprakashNo ratings yet
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- 1.2 - Venn Diagram and Complement of A SetDocument6 pages1.2 - Venn Diagram and Complement of A SetKaden YeoNo ratings yet
- Survey Course OverviewDocument3 pagesSurvey Course OverviewAnil MarsaniNo ratings yet
- ESA Knowlage Sharing - Update (Autosaved)Document20 pagesESA Knowlage Sharing - Update (Autosaved)yared BerhanuNo ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Honda Wave Parts Manual enDocument61 pagesHonda Wave Parts Manual enMurat Kaykun86% (94)
- SD8B 3 Part3Document159 pagesSD8B 3 Part3dan1_sbNo ratings yet
- 15 - 5 - IoT Based Smart HomeDocument6 pages15 - 5 - IoT Based Smart HomeBhaskar Rao PNo ratings yet
- GMWIN SoftwareDocument1 pageGMWIN SoftwareĐào Đình NamNo ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Important Instructions To Examiners:: Calculate The Number of Address Lines Required To Access 16 KB ROMDocument17 pagesImportant Instructions To Examiners:: Calculate The Number of Address Lines Required To Access 16 KB ROMC052 Diksha PawarNo ratings yet
- Numerical Methods Chapter 10 SummaryDocument8 pagesNumerical Methods Chapter 10 SummarynedumpillilNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)