Professional Documents
Culture Documents
Cryptography
Uploaded by
Sky NalinOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cryptography
Uploaded by
Sky NalinCopyright:
Available Formats
Cryptography A network can be secured through device hardening, AAA access control, firewall features, and IPS implementations.
These combined features protect the infrastructure devices as well as the end devices within the local network. But how is network traffic protected when traversing the public Internet? The answer is through cryptographic methods. Secure communications involves a few primary tasks: Authentication - Guarantees that the message is not a forgery and does actually come from who it states it comes from. Integrity - Similar to a checksum function in a frame, guarantees that no one intercepted the message and altered it. Confidentiality - Guarantees that if the message is captured, it cannot be deciphered.
What are the advantages of the system?
The simplest definition available as to, what cryptography is is that it is the science of using mathematics to encrypt and decrypt information, which means putting into or decoding from a mathematical language. What are the ways to use this technology and learn what are advantages? So, as you can see, this seems as though cryptography would be very difficult. Nevertheless, this is important because everything on your computer is stored in cryptography. Cryptography becomes even more complex though. This is because humans recognize numbers as digits from 0 to 9, but your computer can only recognize 0 and 1. As such, this binary system uses bits instead of digits. In order to convert bits to digits you will need to multiply the number of bits by 0.3. This will then provide you with a good estimation of what it stands for. Now there are some other definitions that are important to understand here. First, you should understand that a brute force attack is when all of the possible combinations of numbers are used to either decrypt or encrypt materials. Secondly, a dictionary attack occurs whenever a person tries using all possible known passwords, which is surprisingly a small amount, to form an attack. Of course, there are some people, such as the government, who would profit from knowing cryptography and are thus known as an adversary. On the other hand, those who should not profit from this access are known as a key logger.
All of this probably still sounds very difficult to understand. This is why it takes so much education if you want to work as a cryptographer. There are only some people who can truly understand all of this and thus use it to help all of the rest of us with our daily computer needs. Of course, it is also why the people who work in this field make such good money doing so. Why do you need cryptosystems, Government, private companies and universities exchange data over Internet with their trusted partners? They want full secure data exchange; no hacker or third party should be able to intercept the important data. To over come privacy, secrecy and importance of data being hacked or stolen, cryptography provides two kinds of cryptosystems. First is "Symmetric" system under, which cryptosystems use the same secret key to encrypt or decrypt a message received data packet from trusted partners. The other cryptosystem is asymmetric system under, which two different keys are used to encrypt and decrypt the message or received data packet. On public key is used to encrypt the data or message and the private key on receiving end is used to decrypt the message or data packet. Now the question is how do we send these keys to trusted partners. Other than latest tools used in monitoring, securing data exchange, keys are passed through trusted couriers to avoid data being intercepted by hackers. Encryption - "is a process of changing or converting normal text or data information into gibberish text". Decryption - "is a process of changing or converting gibberish text back to correct message or data by using encryption method". http://www.spywareantivirus.info Article Source: http://EzineArticles.com/?expert=Sanjay_Kak
Article Source: http://EzineArticles.com/839673
Cryptography provides algorithms to keep the message secure while transmitted on Internet. Read more: http://wiki.answers.com/Q/What_are_the_advantages_of_using_cryptography#ixzz1c9bspG4Y
Message privacy Sender and recipient authentication Non-repudiation Anonymity
Fairness Accountability Untraceability Dividability Transferability Off-line operations Universality Data distribution operation (TV, CD-ROM) Selective reception Secrecy in Transmission Secrecy in Storage Integrity in Storage Authentication of Identity
Which protocols they are using/supporting? What are some of their applications?
Secure messaging/mail Secure network communications Network authentication Electronic voting Electronic notary Digital money (digital wallet) or Electronic Cashcards (credit cards, ATM/debit cards) Data distribution Credentialing Systems Electronic Signatures Systems Using Changing Keys Covert communication using Steganogrphy Security mechanisms for secure ID cards, smartcards, biometrics
**( http://electronicsbus.com/cryptography-encryption-algorithms-decryptionnetwork-data-security/)
What is their current status (are they improving or retiring)? What future do you foresee for this technology?
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5784)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (72)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- CD Asia - People V Balasa GR No. 106357Document22 pagesCD Asia - People V Balasa GR No. 106357Therese ElleNo ratings yet
- People v. Quiachon y BayonaDocument1 pagePeople v. Quiachon y BayonaSamuel John CahimatNo ratings yet
- GENSOC ReviewerDocument7 pagesGENSOC ReviewerMaricris MoralesNo ratings yet
- Youth Hong Kong V4N3Document56 pagesYouth Hong Kong V4N3it-adminNo ratings yet
- Summary of Jurisdiction of Philippine CourtsDocument13 pagesSummary of Jurisdiction of Philippine CourtsXavier Hawkins Lopez Zamora82% (17)
- Analytical Study of Protection of Domestic Violence Act 2005Document7 pagesAnalytical Study of Protection of Domestic Violence Act 2005Vasu ThakurNo ratings yet
- Acknowledgement 1703849059383Document4 pagesAcknowledgement 1703849059383vaibhavingle20062006No ratings yet
- Polk County Inmate Roster: Anderson, David Daniel AGE ID Number Booking Date/TimeDocument19 pagesPolk County Inmate Roster: Anderson, David Daniel AGE ID Number Booking Date/TimeDazhit K3No ratings yet
- #TheGame23 Letter From @m1Vr4 N0sce To Staff@Document3 pages#TheGame23 Letter From @m1Vr4 N0sce To Staff@Roth RichchildNo ratings yet
- Qatar Labour Law Legal RegisterDocument32 pagesQatar Labour Law Legal RegisterHadeel Sheikh100% (1)
- Forensic Accounting: Why Companies Should Engage ExpertsDocument32 pagesForensic Accounting: Why Companies Should Engage ExpertsRuth NyawiraNo ratings yet
- Charleston Diocese Priests Accused of Child Sex Crimes (3!29!19)Document4 pagesCharleston Diocese Priests Accused of Child Sex Crimes (3!29!19)ABC News 4No ratings yet
- Escape From The Killing Zone FBI Law Enforcement BulletinDocument8 pagesEscape From The Killing Zone FBI Law Enforcement BulletinKrav Maga TrevisoNo ratings yet
- Use CONTEXT CLUES To Determine The Correct DICTIONARY ENTRYDocument3 pagesUse CONTEXT CLUES To Determine The Correct DICTIONARY ENTRYAriane Zgheia May Castueras0% (1)
- Victim CompensationDocument7 pagesVictim Compensationsri priyaNo ratings yet
- State 911 Response Feb. 7Document2 pagesState 911 Response Feb. 7Melissa HansonNo ratings yet
- The - Police - 2023 - ALL.. 2Document43 pagesThe - Police - 2023 - ALL.. 2Nbch NightNo ratings yet
- Second Amended Complaint USVI JPMDocument119 pagesSecond Amended Complaint USVI JPMCNBC.comNo ratings yet
- Psychological Consequences of Sexual TraumaDocument11 pagesPsychological Consequences of Sexual Traumamary engNo ratings yet
- B.Com Project Report on Corporate FraudDocument26 pagesB.Com Project Report on Corporate FraudNeha jainNo ratings yet
- Cisco Ransomware Defense Validated Design GuideDocument72 pagesCisco Ransomware Defense Validated Design GuideKristine AbanadorNo ratings yet
- United States Court of Appeals, Third Circuit.: Nos. 90-3142, 90-3151 and 90-3152Document28 pagesUnited States Court of Appeals, Third Circuit.: Nos. 90-3142, 90-3151 and 90-3152Scribd Government DocsNo ratings yet
- Constitutional Law 2 Associates - Administrative Due Process and Limitations on Police PowerDocument65 pagesConstitutional Law 2 Associates - Administrative Due Process and Limitations on Police PowermtabcaoNo ratings yet
- Case Digest 18-22Document7 pagesCase Digest 18-22Dona M. ValbuenaNo ratings yet
- Louisville's Response To NOADocument146 pagesLouisville's Response To NOACourier JournalNo ratings yet
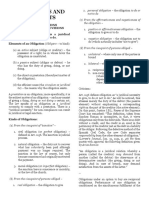
- Oblicon Reviewer First ExamDocument3 pagesOblicon Reviewer First ExamIzzy100% (1)
- DS 3053 Consent For Minors To TravelDocument2 pagesDS 3053 Consent For Minors To TravelMichelle ValenciaNo ratings yet
- Oedipus Rex Answer KeyDocument15 pagesOedipus Rex Answer KeyHannah SmithNo ratings yet
- How Video Games Impact Society and BehaviorDocument71 pagesHow Video Games Impact Society and BehaviorEmico OteroNo ratings yet
- Jeff Wood Trial Transcript, Day 1Document198 pagesJeff Wood Trial Transcript, Day 1TucsonSentinelNo ratings yet