Professional Documents
Culture Documents
6,7,8,9
Uploaded by
nesstleOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
6,7,8,9
Uploaded by
nesstleCopyright:
Available Formats
Page |1 Chapter 6
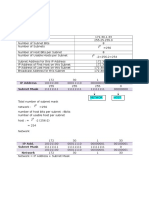
1. Refer to the exhibit. What statement describes the DR/BDR relationship of the HQ router? HQ is the DR. HQ is the BDR. HQ is a DROTHER. HQ is a member of an NBMA network. 2. Which two features are associated with Frame Relay OSPF point-to-multipoint environments? (Choose two.) A DR is not elected. The OSPF priority value determines the active DR on the Frame Relay link. OSPF neighbor routers are statically defined. The link types are identified as broadcast multiaccess. The BDR will have a router ID whose value is greater than the DR router ID. 3. Refer to the exhibit. How was the OSPF default gateway entry for R2 determined? Default routes are automatically injected by OSPF into all advertisements. A static default gateway route is defined in the configuration of R2. The default-information originate command is applied on R1. The ISP defines the gateway of last resort and automatically passes it to R1 and R2. The ip default-gateway command is applied on R2. 4. What is always required for OSPF routers to share routing information? designated routers a backup designated router neighbor adjacencies an NBMA network topology links that are configured on the 224.0.0.0 network 5. Refer to the exhibit. A network administrator has implemented OSPF and the network has converged. If all router interfaces are enabled and functional, what route will OSPF view as lowest cost when moving frames from Host3 to Host1? R3 to R4 to R1 R3 to R1 R3 to R2 to R1 R3 to R5 to R2 to R1
Page |2
6. Refer to the exhibit. Which commands configure router A for OSPF? router ospf 1 network 192.168.10.0 router ospf 1 network 192.168.10.64 0.0.0.63 area 0 network 192.168.10.192 0.0.0.3 area 0 router ospf 1 network 192.168.10.64 255.255.255.192 network 192.168.10.192 255.255.255.252 router ospf 1 network 192.168.10.0 area 0 7. Refer to the exhibit. Which network statement configures the home router to allow all the interfaces to participate in OSPF? network 10.0.0.0 0.3.255.255 area 0 network 10.8.0.0 0.0.0.3 area 0 network 10.8.0.0 0.3.255.255 area 0 network 10.10.0.0 0.0.0.3 area 0 network 10.12.0.0 0.3.255.255 area 0 8. Which statement is true regarding OSPF DR and BDR elections? A new DR/BDR election occurs each time a new OSPF neighbor is added. The router with the highest OSPF priority setting wins the election for DR. The default priority value for a router connected to a multi-access network is 0. The router with the highest MAC address is elected as the DR when the default priority values are used. 9. Refer to the exhibit. The network administrator would like only the 172.16.32.0 network advertised to Router1. Which OSPF network command accomplishes this? Router2(config-router)# network 172.16.0.0 0.0.0.15 area 0 Router2(config-router)# network 172.16.0.0 0.0.15.255 area 0 Router2(config-router)# network 172.16.32.0 0.0.15.255 area 0 Router2(config-router)# network 172.16.32.0 0.0.255.255 area 0 10. Which two statements describe the operation of link-state routing protocols? (Choose two.) All routers in the same area have identical link-state databases when converged. Routing loops are prevented by running the Diffusing Update Algorithm (DUAL). Link-state routers send frequent periodic updates of the entire routing table. Reliable Transport Protocol (RTP) is used to deliver and receive LSAs. Calculating the shortest path for each destination is accomplished with the SPF algorithm.
Page |3
11. Refer to the exhibit. Routers A, B, and C are part of the existing OSPF network. Router D has been added to the network. All routers are running OSPF and have the indicated priorities applied to the interface. What is the DR/BDR status immediately after router D is added to the existing network? An election is forced and router D wins the DR election. The DR and BDR do not change until the next election. An election is forced and the existing BDR becomes the DR. The router with the highest router ID becomes the new BDR. 12. Which two statements describe the use of OSPF DR/BDR elections? (Choose two.) Elections are always optional. Elections are required in all WAN networks. Elections are required in point-to-point networks. Elections are required in broadcast multiaccess networks. Elections are sometimes required in NBMA networks. 13. Refer to the exhibit. As part of an OSPF network, R1 and R2 are trying to become adjacent neighbors. Although it appears that the two systems are communicating, neither of the routing tables include OSPF routes received from its neighbor. What could be responsible for this situation? R1 and R2 are not on the same subnet. The Process IDs on each router do not match. The timer intervals on the routers do not match. The value set for the Transmit Delay time on both routers is too low. 14. Refer to the exhibit. What is the purpose of the value 128 shown in bold? It is the OSPF cost metric. It is the OSPF administrative distance. It is the value assigned by the Dijkstra algorithm that designates the distance in hops to the network. It is the value assigned to an interface that is used by the DUAL algorithm to determine the metric. 15. Refer to the exhibit. What is the purpose of the configuration commands added on router B? allows router A to form an adjacency with router B provides a stable OSPF router ID on router B provides a method of testing router traffic creates the OSPF adjacency table on router B
Page |4
16. Refer to the exhibit. The command ip route 10.16.1.64 255.255.255.252 s0/0/0 is entered into the router. Why does network 10.16.1.64/30 appear in the routing table in addition to network 10.16.1.64/27? The router views 10.16.1.64/30 and 10.16.1.64/27 as two different networks. The static route is used as a backup route for packets destined for 10.16.1.64/27. The AD for static routes is lower than the AD for OSPF routes. The static route metric is lower than the OSPF metric for the 10.16.1.64/27 network. 17. What is the primary difference between link-state protocols and distance vector protocols with regard to route calculation? Distance vector protocols take existing routes from their neighbors and add to them. Link-state protocols independently calculate full routes. Link-state protocols calculate and pass full routing tables to all routers in their associated areas, and distance vector protocols do not. When determining invalid routes, link-state protocols use split horizon for all route computations. Distance vector protocols use reverse poisoning. Distance vector protocols require more CPU and RAM for route calculations than link-state protocols require. 18. What range of networks are advertised in the OSPF updates by the command Router1(config-router)# network 192.168.0.0 0.0.15.255 area 0? 192.168.0.0/24 through 192.168.0.15/24 192.168.0.0/24 through 192.168.15.0/24 192.168.15.0/24 through 192.168.31.0/24 192.168.15.0/24 through 192.168.255.0/24 192.168.16.0/24 through 192.168.255.0/24 19. Refer to the exhibit. When establishing adjacency relationships, which IP address would router A use to send hello packets to router B? 10.11.0.1 10.11.0.2 10.11.0.255 224.0.0.5 255.255.255.255 20. Refer to the exhibit. Which router will be elected the DR and which will become the BDR? R1 will be DR and R2 will be BDR. R1 will be DR and R3 will be BDR. R2 will be DR and R1 will be BDR. R2 will be DR and R3 will be BDR. R3 will be DR and R2 will be BDR. R3 will be DR and R1 will be BDR.
Page |5
21. When compared to a distance vector routing protocol, what is a benefit of the hierarchical design approach that is used in large OSPF networks? simpler configuration reduction of router processing requirements isolation of network instability less complex network planning 22. What are two advantages of using a link-state routing protocol instead of a distance vector routing protocol? (Choose two.) The topology database eliminates the need for a routing table. Frequent periodic updates are sent to minimize the number of incorrect routes in the topological database. Routers have direct knowledge of all links in the network and how they are connected. After the initial LSA flooding, routers generally require less bandwidth to communicate changes in a topology. A link-state routing protocol requires less router processor power. 23. If a network has converged, what is true about the link-state database held by each router in the same OSPF area? Each router has a link-state database containing the same status information. Each router has a different link-state database depending on its position within the network. The link-state database is stored in a designated router and is accessed by each router in the area as needed. The link-state database in each router only contains information about adjacent routers and the status of their links. 24. Refer to the exhibit. RTRC was recently configured and is not sending the proper OSPF routes to RTRB, as shown in the RTRB routing table. Based on the RTRC configuration, what is most likely the problem? RTRC interfaces are administratively shut down. The OSPF process ID for RTRC does not match the process ID used on RTRB. The interface addresses on RTRC overlap with other addresses in the network. The OSPF routing configuration on RTRC has a missing or incorrect network statement.
Page |1 Chapter 7
1. Why are Network Control Protocols used in PPP? to establish and terminate data links to provide authentication capabilities to PPP to manage network congestion and to allow quality testing of the link to allow multiple Layer 3 protocols to operate over the same physical link 2. What is the data transmission rate for the DS0 standard? 44 kb/s 64 kb/s 1.544 Mb/s 44.736 Mb/s 3. In which two layers of the OSI model are key differences found between a LAN and a WAN. (Choose two.) Layer 1 Layer 2 Layer 3 Layer 4 Layer 6 Layer 7 4. Which statement is true about the Cisco implementation of the HDLC protocol? It supports authentication. It has a universally compatible frame format. It is the default encapsulation for serial interfaces on Cisco routers. It does not support multiple protocols across a single link. 5. Refer to the exhibit. A network administrator has a connectivity problem between the serial interfaces of Merida and Vargas. What is the cause of the problem? Authentication is required on the serial link. The encapsulation is misconfigured. The IP addresses are on different subnets. The serial interface on Vargas is shutdown. The loopback interfaces on both routers are not configured. 6. Refer to the exhibit. What statement is true about the exhibited output? LCP is in the process of negotiating a link. LCP and NCP are waiting for CHAP authentication to complete. LCP negotiation has completed successfully, but NCP negotiation is in progress. LCP and NCP negotiation is complete, and the data link service is available to carry packets.
Page |2
7. Which three statements are true regarding LCP? (Choose three.) It is responsible for negotiating link establishment. It negotiates options for Layer 3 protocols running over PPP. It uses MD5 encryption while negotiating link-establishment parameters. It terminates the link upon user request or the expiration of an inactivity timer. It can test the link to determine if link quality is sufficient to bring up the link. It monitors the link for congestion and dynamically adjusts the acceptable window size. 8. Why are Frame Relay paths referred to as virtual? Frame Relay PVCs are created and discarded on demand. The connections between PVC endpoints act like dialup circuits. There are no dedicated circuits to and from the Frame Relay carrier. The physical circuits inside the Frame Relay cloud do not contain exclusive links for a specific Frame Relay connection. 9. What best describes the use of a data-link connection identifier (DLCI)? an address identifying a virtual circuit a logical address identifying the DCE device an address identifying a Layer 3 service across a Frame Relay network a logical address identifying the physical interface between a router and a Frame Relay switch 10. What two services allow the router to dynamically map data link layer addresses to network layer addresses Frame Relay network? (Choose two.) ARP ICMP Proxy ARP Inverse ARP LMI status messages 11. Which three statements describe functions of the Point-to-Point Protocol with regards to the OSI model?(Choose three.) operates at all layers of the OSI model provides a mechanism to multiplex several network layer protocols can be configured on both synchronous and asynchronous serial interfaces uses Layer 3 of the OSI model to establish and maintain a session between devices uses the data link layer to configure such options as error detection and compression uses network control protocols to test and maintain connectivity between devices 12. At what physical location does the responsibility for a WAN connection change from the user to the service provider? demilitarized zone (DMZ) demarcation point local loop cloud
Page |3
13. What does a Frame Relay switch use to inform the sender that there is congestion? FECN BECN DE FCS 14. Refer to the exhibit. What statement is true about the debug output? R2 is using PAP instead of CHAP. The routers have different CHAP passwords configured. The administrator performed a shutdown on the R2 PPP interface during negotiation. The Layer 3 protocol negotiation caused the connection failure. 15. Which two statements describe the function of time-division multiplexing? (Choose two.) Multiple data streams share one common channel. Conversations that require extra bandwidth receive any unused time slices. Time slots are utilized on a first-come, first-served basis. Time slots go unused if a sender has nothing to transmit. Priority can be dedicated to one data source. 16. When customers use credit cards to make purchases at a small business, a modem is heard dialing a telephone number to transfer the transaction data to the central office. What type of WAN serial connection is in use? leased line point-to-point circuit switched packet switched 17. Which best describes data communications equipment (DCE)? serves as data source and/or destination responsible for negotiating windowing and acknowledgements physical devices such as protocol translators and multiplexers equipment that forwards data and is responsible for the clocking signal 18. Permanent virtual circuits and switched virtual circuits are both part of which option for WAN connectivity? leased line cell switching packet switching circuit switching
Page |4
19. Which field of a frame uses error detection mechanisms to verify that the frame is not damaged intransit? FCS MTU flag control protocol 20. What occurs in the encapsulation process as a data packet moves from a LAN across a WAN? The Layer 2 encapsulation changes to a format that is appropriate for the WAN technology. The Layer 3 encapsulation changes to a format that is appropriate for the WAN technology. Both Layer 2 and Layer 3 encapsulation change to a technology that is appropriate for the WAN. Both Layer 2 and Layer 3 encapsulation remain constant as the data packet travels throughout the network. 21. Refer to the exhibit. The network administrator is configuring R1 to connect to R2, which is a non-Cisco router. Which encapsulation method will need to be configured for communication to occur? HDLC HSSI ISDN IPCP PPP 22. A company is implementing dialup services for remote workers to connect to the local network. The company uses multiple Layer 3 protocols and requires authentication for security. Which protocol should be used for this remote access? LMI PPP HDLC Frame Relay 23. Which two options can LCP negotiate? (Choose two.) compression authentication dynamic flow control network layer address for IP connection-oriented or connectionless communication methods 24. What statement best describes cell switching? It uses a dedicated path between endpoints. It creates a permanent physical link between two points. It uses DLCIs to identify virtual circuits. It creates fixed-length packets that traverse virtual circuits.
Page |1 Chapter 8
1. Refer to the exhibit. A network administrator needs to add the command deny ip 10.0.0.0 0.255.255.255 any log to R3. After adding the command, the administrator verifies the change using the show access-list command. What sequence number does the new entry have? 0 10, and all other items are shifted down to the next sequence number 50 60 2. Refer to the exhibit. What happens if the network administrator issues the commands shown when an ACL called Managers already exists on the router? The new commands overwrite the current Managers ACL. The new commands are added to the end of the current Managers ACL. The new commands are added to the beginning of the current Managers ACL. An error appears stating that the ACL already exists. 3. Why are inbound ACLs more efficient for the router than outbound ACLs? Inbound ACLs deny packets before routing lookups are required. Inbound ACL operation requires less network bandwidth than outbound. Inbound ACLs permit or deny packets to LANs, which are typically more efficient than WANs Inbound ACLs are applied to Ethernet interfaces, while outbound ACLs are applied to slower serial interfaces. 4. Refer to the exhibit. The network administrator of a company needs to configure the router RTA to allow its business partner (Partner A) to access the web server located in the internal network. The web server is assigned a private IP address, and a static NAT is configured on the router for its public IP address. Finally, the administrator adds the ACL. However, Partner A is denied access to the web server. What is the cause of the problem? Port 80 should be specified in the ACL. The public IP address of the server, 209.165.201.5, should be specified as the destination. The ACL should be applied on the s0/0 outbound interface. The source address should be specified as 198.133.219.0 255.255.255.0 in the ACL. 5. ACL logging generates what type of syslog message? unstable network warning informational critical situation
Page |2
6. Which two host addresses are included in the range specified by 172.16.31.64 0.0.0.31? (Choose two.) 172.16.31.64 172.16.31.77 172.16.31.78 172.16.31.95 172.16.31.96 7. Traffic from the 64.104.48.0 to 64.104.63.255 range must be denied access to the network. What wildcard mask would the network administrator configure in the access list to cover this range? 0.0.15.255 0.0.47.255 0.0.63.255 255.255.240.0 8. ACLs are used primarily to filter traffic. What are two additional uses of ACLs? (Choose two.) specifying source addresses for authentication specifying internal hosts for NAT identifying traffic for QoS reorganizing traffic into VLANs filtering VTP packets 9. What can an administrator do to ensure that ICMP DoS attacks from the outside are mitigated as much as possible, without hampering connectivity tests initiated from the inside out? Create an access list permitting only echo reply and destination unreachable packets from the outside. Create an access list denying all ICMP traffic coming from the outside. Permit ICMP traffic from only known external sources. Create an access list with the established keyword at the end of the line. 10. What effect does the command reload in 30 have when entered into a router? If a router process freezes, the router reloads automatically. If a packet from a denied source attempts to enter an interface where an ACL is applied, the router reloads in 30 minutes. If a remote connection lasts for longer than 30 minutes, the router forces the remote user off. A router automatically reloads in 30 minutes.
Page |3
11. Refer to the exhibit. The following commands were entered on RTB. RTB(config)# access-list 4 deny 192.168.20.16 0.0.0.15 RTB(config)# access-list 4 permit any RTB(config)# interface serial 0/0/0 RTB(config-if)# ip access-group 4 in Which addresses do these commands block access to RTB? 192.168.20.17 to 192.168.20.31 192.168.20.16 to 192.168.20.31 192.168.20.16 to 192.168.20.32 192.168.20.16 to 192.168.20.33 12. Refer to the exhibit. The new security policy for the company allows all IP traffic from the Engineering LAN to the Internet while only web traffic from the Marketing LAN is allowed to the Internet. Which ACL can be applied in the outbound direction of Serial 0/1 on the Marketing router to implement the new security policy? access-list 197 permit ip 192.0.2.0 0.0.0.255 any access-list 197 permit ip 198.18.112.0 0.0.0.255 any eq www access-list 165 permit ip 192.0.2.0 0.0.0.255 any access-list 165 permit tcp 198.18.112.0 0.0.0.255 any eq www access-list 165 permit ip any any access-list 137 permit ip 192.0.2.0 0.0.0.255 any access-list 137 permit tcp 198.18.112.0 0.0.0.255 any eq www access-list 89 permit 192.0.2.0 0.0.0.255 any access-list 89 permit tcp 198.18.112.0 0.0.0.255 any eq www 13. Which three statements are true concerning standard and extended ACLs? (Choose three.) Extended ACLs are usually placed so that all packets go through the network and are filtered at the destination. Standard ACLs are usually placed so that all packets go through the network and are filtered at the destination. Extended ACLs filter based on source address only, and must be placed near the destination if other traffic is to flow. Standard ACLs filter based on source address only, and must be placed near the destination if other traffic is to flow. Extended ACLs filter with many possible factors, and they allow only desired packets to pass through the network if placed near the source. Standard ACLs filter with many possible factors, and they allow only desired packets to pass through the network if placed near the source.
Page |4
14. Refer to the exhibit. Company policy for the network that is shown indicates the following guidelines: 1) All hosts on the 192.168.3.0/24 network, except host 192.168.3.77, should be able to reach the 192.168.2.0/24 network. 2) All hosts on the 192.168.3.0/24 network should be able to reach the 192.168.1.0/24 network. 3) All other traffic originating from the 192.168.3.0 network should be denied. Which set of ACL statements meets the stated requirements when they are applied to the Fa0/0 interface of router R2 in the inbound direction? access-list 101 deny ip any any access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255 access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255 access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255 access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255 access-list 101 permit ip any any access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255 access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.0.0 0.0.255.255 15. Hosts from the Limerick LAN are not allowed access to the Shannon LAN but should be able to access the Internet. Which set of commands will create a standard ACL that will apply to traffic on the Shannon router interface Fa0/0 implementing this security? access-list 42 deny 172.19.123.0 0.0.0.255 192.0.2.0 0.0.0.255 access-list 42 permit any access-list 56 deny 172.19.123.0 0.0.0.255 access-list 56 permit any access-list 61 deny 172.19.123.0 0.0.0.0 access-list 61 permit any access-list 87 deny ip any 192.0.2.0 0.0.0.255 access-list 87 permit ip any
Page |5
16. Refer to the exhibit. A network administrator needs to configure an access list that will allow the management host with an IP address of 192.168.10.25/24 to be the only host to remotely access and configure router RTA. All vty and enable passwords are configured on the router. Which group of commands will accomplish this task? Router(config)# access-list 101 permit tcp any 192.168.10.25 0.0.0.0 eq telnet Router(config)# access-list 101 deny ip any any Router(config)# int s0/0 Router(config-if)# ip access-group 101 in Router(config-if)# int fa0/0 Router(config-if)#ip access-group 101 in Router(config)# access-list 10 permit 192.168.10.25 eq telnet Router(config)# access-list 10 deny any Router(config)# line vty 0 4 Router(config-line)#access-group 10 in Router(config)# access-list 86 permit host 192.168.10.25 Router(config)# line vty 0 4 Router(config-line)# access-class 86 in Router(config)# access-list 125 permit tcp 192.168.10.25 any eq telnet Router(config)# access-list 125 deny ip any any Router(config)# int s0/0 Router(config-if)# ip access-group 125 in 17. Which ACL permits host 10.220.158.10 access to the web server 192.168.3.244? access-list 101 permit tcp host 10.220.158.10 eq 80 host 192.168.3.224 access-list 101 permit tcp 10.220.158.10 0.0.0.0 host 192.168.3.224 0.0.0.0 eq 80 access-list 101 permit host 10.220.158.10 0.0.0.0 host 192.168.3.224 0.0.0.0 eq 80 access-list 101 permit tcp 10.220.158.10 0.0.0.0 host 192.168.3.224 eq 80 18. Which wildcard mask would match the host range for the subnet 192.16.5.32 /27? 0.0.0.32 0.0.0.63 0.0.63.255 0.0.0.31 19. A security administrator wants to secure password exchanges on the vty lines on all routers in the enterprise. What option should be implemented to ensure that passwords are not sent in clear text across the public network? Use Telnet with an authentication server to ensure effective authentication. Apply an access list on the router interfaces to allow only authorized computers. Apply an access list on the vty line to allow only authorized computers. Use only Secure Shell (SSH) on the vty lines.
Page |6
20. Refer to the exhibit. An administrator notes a significant increase in the amount of traffic entering the network from the ISP. The administrator clears the access-list counters. After a few minutes, the administrator again checks the access-list table. What can be concluded from the most recent output shown? A small amount of HTTP trafic is an indication that the web server was not configured correctly. A larger amount of POP3 traffic (compared with SMTP traffic) indicates that there are more POP3 email clients than SMTP clients in the enterprise. A large amount of ICMP traffic is being denied at the interface, which can be an indication of a DoS attack. A larger amount of email traffic (compared with web traffic) is an indication that attackers mainly targeted the email server.
Page |1 Chapter 9
1. Refer to the exhibit. Based on the output shown, to which IP network should the workstations in the Support department belong? 192.168.1.0 172.16.1.0 172.16.3.0 172.16.5.0 2. Refer to the exhibit. A network administrator is doing proactive network maintenance. The administrator pings 192.168.1.100 and compares the results to the baseline data. Based on the comparison of the two pings, what is one possibility? There is an ACL applied, making the destination host unreachable. There is a malfunctioning NIC on the destination host. The sending host is unable to access the network. There are congestion problems on the network. 3. Refer to the exhibit. Given the output generated by the debug ppp negotiation command, which statement is true? The line protocol of the local router is now up. The username Goleta is configured locally. The command ppp authentication pap is configured on both routers. The local router requested to terminate the session. 4. What is important to consider while configuring the subinterfaces of a router when implementing inter-VLAN routing? The subinterface numbers must match the VLAN ID number. The physical interface must have an IP address configured. The IP address of each subinterface must be the default gateway address for each VLAN subnet. The no shutdown command must be given on each subinterface. 5. Refer to the exhibit. A lab technician connects two routers together via a serial cable using the default interface configuration values. The interfaces are up; however, the technician is unable to ping between the two devices. What is the most likely problem? The lab technician used the wrong cable to connect the serial ports. There is an IP mismatch between the serial ports. There is an encapsulation mismatch between the serial ports. No clock rate has been set on the DCE interface.
Page |2
6. Refer to the exhibit. Based on the output shown, why is VTP information unable to propagate the network? One of the two client mode switches must be reconfigured to Transparent mode. Each switch must be synchronized to the network time server. The VTP domain names are different. VTP passwords must be set. The configuration revision numbers are all the same. 7. The enterprise mail server software recently went through a minor update. A network administrator notices an excessive amount of traffic between a database server and the newly updated mail server, compared to the baseline data. What is the first action the administrator should do to investigate the problem? Wait to see if the recent update will stabilize after a while. Redo the baseline data to include the minor upgrade. Check the log to see what software components are producing the excess traffic. Check for viruses and spyware on the database server. 8. Refer to the exhibit. Users are reporting that they cannot access the Internet. Routers R1 and R2 are configured with RIP version 2 as shown. If R2 receives a packet with a destination address on the Internet, how is the packet routed? The packet is routed to the ISP router and then to network 10.1.1.0/24. The packet is routed to the ISP router and then to the Internet. The packet is routed to R1 and then forwarded out Fa0/0 on R1. The packet will not be routed because R2 does not have a valid default route. 9. Refer to the exhibit. Both routers are configured using RIPv1. Both routers are sending updates about the directly connected routes. R1 can successfully ping the serial interface of R2. The routing table on R1 does not contain any dynamically learned routes from R2, and the routing table on R2 shows no dynamically learned routes from R1. What is the problem? Subnetting is not supported by RIPv1. One of the routers needs a clock rate on the serial interface. The serial link between the two routers is unstable. VLSM is not supported by RIPv1. 10. Refer to the exhibit. Host 192.168.1.14 is unable to download email from 192.168.2.200. After reviewing the output of the show running-config command, what problem is discovered? Access to the SMTP server is denied. The destination host address in an ACL statement is incorrect. The ACL is applied to the interface in the wrong direction. The implicit deny any any is blocking all access to email.
Page |3
11. An employee called the help desk to report a laptop that could not access a web-based application on the Internet. The help desk technician asked the employee to open a Windows command prompt and type the ipconfig /all command. Which problem-solving technique did the technician choose? top-down bottom-up substitution divide-and-conquer 12. Refer to the exhibit. Based on the network diagram and the output shown, which statement is true? The command was entered on router R1. The command was entered on router R2. The command was entered on router R3. The command could have been entered on either R1 or R2. 13. Refer to the exhibit. An ACL is configured to prevent access by network 192.168.1.0 to network 192.168.2.0, but it is not working properly. What problem is discovered after observing the output of the show running-config command? The protocol type specified in the ACL should be TCP, not IP. The source and destination addresses are reversed in the statement. The ACL is applied to the wrong interface, but the right direction. The ACL is applied to the wrong interface and the wrong direction. The permit ip any any statement allows network 192.168.1.0 access. 14. Although all networks are reachable, the network administrator notices abnormal routing behavior after configuring OSPF on each router. According to the partial output from the debug ip ospf events command, which statement is true about the contents of the routing table in RA? It will show network 172.16.3.0 learned from RB. It will show network 172.16.3.0 learned from RC. It will show two equal routes to network 192.168.1.4/30. It will show two equal routes to network 192.168.1.8/30. 15. A network at a large building failed, causing a severe disruption in business activities. The problem was eventually detected and resolved by replacing a piece of failed network equipment. Investigation led to the conclusion that a network design problem was the main cause of the disruption. Loss of a single piece of equipment should not have been able to cause such a large problem. What two terms best describe this type of design weakness? (Choose two.) bottleneck limited availability limited scalability large failure domain single point of failure limited staff capabilities
Page |4
16. Refer to the exhibit. The network administrator is troubleshooting the connectivity issue between RA and RB. According to the partial configuration, what is the cause of the problem? password mismatch for PPP authentication username mismatch for PPP authentication encapsulation method mismatch for PPP authentication authentication method mismatch for PPP authentication 17. Refer to the exhibit. ABC Company is using the 172.16.0.0/18 network. It is standard company practice to use the first 50 addresses for switches and servers and assign the last usable address to the router. The remaining addresses are assigned to the hosts. After assigning the addresses, the network technician tests connectivity from the host above and is not able to ping the router. What could be the problem? The router was assigned the broadcast address. The host is not in the same subnet as the switch and router. The router interface is in the wrong subnet. The host was assigned a network address. 18. Refer to the exhibit. A network administrator is troubleshooting a problem. No users are able to access the 10.10.2.0/24 network, but are able to access all other networks. Assuming R3 is configured correctly and based on the output shown, what is most likely the problem? There is congestion on the 10.10.2.0 network. The EIGRP process number on R2 is incorrect. The Fa0/0 interface on R2 is shut down. The Fa0/0 interface on R2 has an incorrect IP address or subnet mask. 19. Refer to the exhibit. The network administrator correctly configures RTA to perform inter-VLAN routing. Using the show vlan command, the administrator verifies that port Fast Ethernet 0/4 is the first available port in the default VLAN on SW2. The administrator connects RTA to port 0/4 on SW2, but inter-VLAN routing does not work. What could be the possible cause of the problem with the SW2 configuration? Port 0/4 is not active. Port 0/4 must be a member of VLAN1. Port 0/4 is configured in access mode. Port 0/4 is configured as a trunk port. 20. Refer to the exhibit. The network administrator is unable to ping from the console of router R3 to host 10.10.4.63. What is the problem? RIPv1 does not support VLSM. Router R2 does not have RIP correctly configured. Router R3 is missing a network statement for network 10.0.0.0. There is an addressing problem on the link between routers R2 and R3.
Page |5
21. Refer to the exhibit. A network administrator has implemented subnetting using the network 192.168.25.0 and a /28 mask. Workstation 1 is not able to ping with Workstation 2. What is a possible cause for this lack of communication? Workstation 1 and Workstation 2 are on the same subnet. The serial connections are using addresses from the LAN subnets. All hosts in the network must be in the same subnet to communicate. Workstation 1 is not on the same network that the RTA router LAN interface is on. 22. Which two statements describe when a network administrator should perform a network baseline? (Choose two.) It should be done monthly as a minimum standard. It should be performed when all switch Cisco IOS versions are upgraded. It should be done when all network printers are upgraded to a new model. It should be done when the network is performing at normal activity levels. It should be done whenever an SLA has been signed with a new service provider.
You might also like
- Lunar Roving VehicleDocument14 pagesLunar Roving VehicleBob AndrepontNo ratings yet
- The history of money from its origins to modern timesDocument22 pagesThe history of money from its origins to modern timesLulu RacpanNo ratings yet
- WEC Engineer 1968Document7 pagesWEC Engineer 1968nesstleNo ratings yet
- Living With A StarDocument24 pagesLiving With A StarnesstleNo ratings yet
- Principles For Financial Market InfrastructuresDocument188 pagesPrinciples For Financial Market InfrastructuresAlice WijnenNo ratings yet
- Medicines Made EasyDocument40 pagesMedicines Made EasynesstleNo ratings yet
- Financial Market FinalDocument327 pagesFinancial Market Finalvarshadumbre100% (3)
- Tesla2005 17Document76 pagesTesla2005 17nesstleNo ratings yet
- Star Child 5Document27 pagesStar Child 51sdaasfdasNo ratings yet
- Trends in Spending-ReportDocument48 pagesTrends in Spending-ReportnesstleNo ratings yet
- Power Money and SexDocument157 pagesPower Money and SexnesstleNo ratings yet
- Isaac Unterman, The Talmud. An Analytical Guide To Its History and TeachingsDocument367 pagesIsaac Unterman, The Talmud. An Analytical Guide To Its History and TeachingsBibliotheca midrasicotargumicaneotestamentariaNo ratings yet
- Revolution Starts at HomeDocument111 pagesRevolution Starts at HomeMichaela Wagner100% (2)
- Money Laundering Through The Football Sector: FATF ReportDocument42 pagesMoney Laundering Through The Football Sector: FATF Reportmikelowrey779No ratings yet
- Money Monthly StatisticsDocument6 pagesMoney Monthly StatisticsnesstleNo ratings yet
- A Field Guide For Painting, Home Maintenance, and Renovation WorkDocument84 pagesA Field Guide For Painting, Home Maintenance, and Renovation Worksai_raghava1No ratings yet
- Healing With The Medicine of The ProphetDocument652 pagesHealing With The Medicine of The Prophetahmed.ne7970No ratings yet
- Media EducationDocument14 pagesMedia EducationnesstleNo ratings yet
- Sport AuthorityDocument12 pagesSport AuthoritynesstleNo ratings yet
- A Quick Guide To The 5 Elements - Stephanie RobertsDocument14 pagesA Quick Guide To The 5 Elements - Stephanie Robertssrce100% (4)
- Medicine: Research in SportsDocument1 pageMedicine: Research in SportsnesstleNo ratings yet
- Human ResourcesDocument3 pagesHuman ResourcesnesstleNo ratings yet
- Careers in Finance GuideDocument6 pagesCareers in Finance GuidenesstleNo ratings yet
- Comparative Sports StudiesDocument18 pagesComparative Sports StudiesnesstleNo ratings yet
- SPORTS STUDIES COURSES OFFERED LESS FREQUENTLYDocument3 pagesSPORTS STUDIES COURSES OFFERED LESS FREQUENTLYnesstleNo ratings yet
- Saunders ExDocument11 pagesSaunders ExnesstleNo ratings yet
- 3 R CGUE9 Pe FQCDocument82 pages3 R CGUE9 Pe FQCnesstleNo ratings yet
- JEPDocument22 pagesJEPgptsgrNo ratings yet
- FinalDocument23 pagesFinalnesstleNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5782)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (72)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Ewb-E100 VPNDocument4 pagesEwb-E100 VPNAntonio CamposNo ratings yet
- FDFDSFDocument15 pagesFDFDSFAnderson Nuñez SaldañaNo ratings yet
- Assigment Sheet Tast 2 Aina MardianaDocument10 pagesAssigment Sheet Tast 2 Aina MardianaAina MardianaNo ratings yet
- 1.1.1.5 Lab - Cybersecurity Case StudiesDocument2 pages1.1.1.5 Lab - Cybersecurity Case Studiesc583706No ratings yet
- Lab 5 - OSPF Full LabDocument21 pagesLab 5 - OSPF Full LabCésar CastilloNo ratings yet
- Speaking Worksheet: Don'T Be A Victim To Online Scams!Document1 pageSpeaking Worksheet: Don'T Be A Victim To Online Scams!Juan BolivarNo ratings yet
- MES series Ethernet switches deliver advanced L2+ features and securityDocument5 pagesMES series Ethernet switches deliver advanced L2+ features and securityantonije44No ratings yet
- Layer 3 Routing On MLSDocument18 pagesLayer 3 Routing On MLSKuldeep DidwaniaNo ratings yet
- BRKSEC-3172 Advanced IOS XR SecurityDocument70 pagesBRKSEC-3172 Advanced IOS XR Securityreferenceref31No ratings yet
- BRKCOL 2060bDocument46 pagesBRKCOL 2060bLA-ZOUBE GAELNo ratings yet
- Internet in TRB EXAMDocument120 pagesInternet in TRB EXAMSiva JiNo ratings yet
- Atcom Phone ManualDocument47 pagesAtcom Phone ManualJaneNo ratings yet
- Constructive Tensions in Feminist Technology Studies: Social Studies of Science December 2000Document24 pagesConstructive Tensions in Feminist Technology Studies: Social Studies of Science December 2000Raquel IsidoroNo ratings yet
- Facebook user feedback formDocument2 pagesFacebook user feedback formgowtham52975% (12)
- VPC LabDocument4 pagesVPC LabsaketsjNo ratings yet
- Assignment 2Document7 pagesAssignment 2Mohammed AliNo ratings yet
- Week6 Chap15 WirelessLANsDocument34 pagesWeek6 Chap15 WirelessLANsBashayer .KNo ratings yet
- VLAN Configuration via CLI on 300/500 Series Managed SwitchesDocument4 pagesVLAN Configuration via CLI on 300/500 Series Managed Switchesreferenceref31No ratings yet
- Classful IP Addressing (Cont.) : Address Prefix Address SuffixDocument25 pagesClassful IP Addressing (Cont.) : Address Prefix Address SuffixGetachew ShambelNo ratings yet
- AZ 700 v22.6.2 - 85 Zg4fyeDocument119 pagesAZ 700 v22.6.2 - 85 Zg4fyeEdoardo NalinNo ratings yet
- Computer Networks: Instructor: Kalyan Sasidhar P S Associate Professor, FB 2109 Kalyan - Sasidhar@daiict - Ac.inDocument28 pagesComputer Networks: Instructor: Kalyan Sasidhar P S Associate Professor, FB 2109 Kalyan - Sasidhar@daiict - Ac.inHeet MistryNo ratings yet
- 07 MulticastDocument139 pages07 MulticastashwinlamroiaNo ratings yet
- Infallible and Upgradable Geo-Environment Based Multicasting Protocol in ManetsDocument5 pagesInfallible and Upgradable Geo-Environment Based Multicasting Protocol in Manetssurendiran123No ratings yet
- Social MediaDocument4 pagesSocial MediaVince DaymielNo ratings yet
- CCNA, Fundamental & Routing PDFDocument49 pagesCCNA, Fundamental & Routing PDFbobmarc100% (1)
- Network Design and ImplementationDocument12 pagesNetwork Design and ImplementationCan Khuong Duy (BTEC HN)No ratings yet
- What's in a Domain NameDocument17 pagesWhat's in a Domain NameRyda SNo ratings yet
- Next Generation Gigabit Residential Gateway For FTTH and Lan NetworksDocument2 pagesNext Generation Gigabit Residential Gateway For FTTH and Lan NetworksJaime CaicedoNo ratings yet
- Assignment 2Document4 pagesAssignment 2LaDonna WhiteNo ratings yet
- Deepak Ram: Curriculum VitaeDocument3 pagesDeepak Ram: Curriculum VitaeDeepak KumarNo ratings yet