Professional Documents
Culture Documents
ISMS Workpractice
Uploaded by
水雲0 ratings0% found this document useful (0 votes)
135 views10 pagesISMS
Original Title
ISMS Workpractice.ppt
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PPT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentISMS
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
135 views10 pagesISMS Workpractice
Uploaded by
水雲ISMS
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
You are on page 1of 10
Information Security Management System
Information & Information Security
Information is an asset Essential Asset to meet Organizations Business Objectives Information Security is the protection of Confidentiality Integrity & Availability
Why Information Security
Business Interconnectivity Need Of Time More interconnectivity = Information is exposed to more audience More exposure = Information exposed to more varieties of Threats & Vulnerabilities Business Impacts on realization of threat Loss of Business, Legal actions, disrepute
Implementing Information Security
Identify the Security Requirements of the organization
Business Objectives
Legal Statutory Requirements
Contractual Requirements
Implementing Information Security
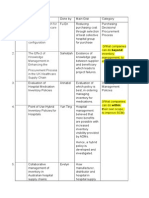
Selecting Controls Controls to be implemented selected based on Security Requirement Analysis Implementing Controls Organizational Policy Procedures Reviewing Controls Testing controls ( e.g. Vulnerability Assessment, Penetration Testing etc) Review as part of incident response (e.g. Virus attack, Hacker attack etc) Periodic Internal Audits
How may we help you
Consulting Services Information Security Management System (ISMS) BS 7799 (ISO 27001) BS 7799 (ISO 27001) Gap Analysis Information Security Policies & Procedures Formulation Risk Assessment Business Continuity Plan (BCP) Disaster Recovery Plan (DRP) Control Objectives for Information and Related Technology (COBIT)
How may we help you
Technical Services
Vulnerability Assessment & Penetration Testing Network Security Architecture Review & Design Technical Audit Application Security Testing Wireless Security Audit Computer Forensics Desktop Audit
How may we help you
Managed Security Services - as per clients security policy
Defining Security Policies for different security components. Identifying vulnerabilities and the risks Alerts and counter measure for potential threats. Log & Event Analysis. Pattern Monitoring and Intrusion trend Analysis Implementation of patches & upgrades Update of latest signatures for IDS and Anti-virus Incident Management Periodic audits Review organizations security policy Prepare activity list as per the organization security policy Monitor and review the implementation of policies. Incident Management Suggesting corrective and preventive measures Presentation to the steering committee Identify improvements in the ISMS and implement recommendations
Question Answer Session
Thank You !!
You might also like
- Maurice Ravel - Piano Concerto in GDocument95 pagesMaurice Ravel - Piano Concerto in G水雲No ratings yet
- Maurice Ravel - Piano TrioDocument35 pagesMaurice Ravel - Piano Trio水雲100% (5)
- Maurice Ravel - Pavane For Dead PrincessDocument4 pagesMaurice Ravel - Pavane For Dead Princess水雲75% (8)
- Take 5 - Paul DesmondDocument1 pageTake 5 - Paul Desmond水雲No ratings yet
- Jean-Louis Streabbog - 12 Easy PiecesDocument28 pagesJean-Louis Streabbog - 12 Easy Pieces水雲100% (1)
- Maurice Ravel - Piano PreludeDocument2 pagesMaurice Ravel - Piano Prelude水雲100% (9)
- Handel 12 Easy PiecesDocument25 pagesHandel 12 Easy Piecesfernanda romero100% (3)
- Charles-Valentin Alkan, The Preludes, Op. 31 Part 18Document4 pagesCharles-Valentin Alkan, The Preludes, Op. 31 Part 18水雲No ratings yet
- Mozart Piano Sonata K533Document20 pagesMozart Piano Sonata K533ah_singNo ratings yet
- Webu Sayadaw - The Way To Ultimate CalmDocument252 pagesWebu Sayadaw - The Way To Ultimate Calm水雲100% (2)
- H. Berens - Op. 70 - 50 Piano Pieces For BeginnersDocument19 pagesH. Berens - Op. 70 - 50 Piano Pieces For BeginnersHoward LockwardNo ratings yet
- IMSLP00215-Mozart - Piano Sonata K 284Document24 pagesIMSLP00215-Mozart - Piano Sonata K 284José Miguel Román100% (1)
- Joseph Haydn Piano Sonata No 34 in E MinorDocument11 pagesJoseph Haydn Piano Sonata No 34 in E Minordabe dabeNo ratings yet
- Satipatthana - The Direct Path To RealizationDocument336 pagesSatipatthana - The Direct Path To Realization水雲No ratings yet
- Mozart Sonata KV 333Document20 pagesMozart Sonata KV 333Gervan SealyNo ratings yet
- Mozart - Piano Sonata No. 17 in B-Flat Major, K. 570Document19 pagesMozart - Piano Sonata No. 17 in B-Flat Major, K. 570水雲No ratings yet
- Mozart Piano Sonata K 457Document14 pagesMozart Piano Sonata K 457Teofano AlsbergNo ratings yet
- Mozart - Piano Sonata No. 18 in D (K576)Document16 pagesMozart - Piano Sonata No. 18 in D (K576)api-26524081100% (2)
- Mozart Piano Sonata K 279Document12 pagesMozart Piano Sonata K 279Diana PerezNo ratings yet
- Mozart Piano Sonata K 547aDocument9 pagesMozart Piano Sonata K 547aJanice KrookNo ratings yet
- Mozart Piano Sonata K 282Document8 pagesMozart Piano Sonata K 282Vlad CiupituNo ratings yet
- CPE Bach - Trio Sonata in B MajorDocument12 pagesCPE Bach - Trio Sonata in B Major水雲No ratings yet
- Mozart Sonata K 281Document16 pagesMozart Sonata K 281Bill-ay LaPietraNo ratings yet
- Mozart Piano Sonata K 330Document14 pagesMozart Piano Sonata K 330Bessie JiangNo ratings yet
- IMSLP00216-Mozart - Piano Sonata K 309Document19 pagesIMSLP00216-Mozart - Piano Sonata K 309Luka RadovicNo ratings yet
- Mozart Piano Sonata K 310Document20 pagesMozart Piano Sonata K 310rox13khNo ratings yet
- Mozart - Piano Sonata No.9 in D Major, K.311Document18 pagesMozart - Piano Sonata No.9 in D Major, K.311水雲No ratings yet
- Schumann - Op.68 - 30 Untitled in F Major.Document2 pagesSchumann - Op.68 - 30 Untitled in F Major.水雲No ratings yet
- CPE Bach - Trio Sonata in G MajorDocument24 pagesCPE Bach - Trio Sonata in G Major水雲100% (1)
- Schumann - Op.68 - 42 Figurierter Choral in F MajorDocument2 pagesSchumann - Op.68 - 42 Figurierter Choral in F Major水雲No ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- PCF Consumer Electronics Ver 6.0.0Document35 pagesPCF Consumer Electronics Ver 6.0.0carebeardancer5678No ratings yet
- Supply Chain ManagementDocument15 pagesSupply Chain ManagementAankit Kumar Jain Dugar100% (1)
- Talitay, MaguindanaoDocument2 pagesTalitay, MaguindanaoSunStar Philippine NewsNo ratings yet
- Business Team ResponsibilitiesDocument3 pagesBusiness Team ResponsibilitiesKz AwangNo ratings yet
- Tata Final File 15th May 2021Document3 pagesTata Final File 15th May 2021Deep sharmaNo ratings yet
- Sablayan, Occidental MindoroDocument2 pagesSablayan, Occidental MindoroSunStar Philippine NewsNo ratings yet
- COBIT Checklist and ReviewDocument20 pagesCOBIT Checklist and ReviewMike0% (1)
- Recruitment and Selection Process Sachin KadlakDocument11 pagesRecruitment and Selection Process Sachin KadlakAfzal PetiwalaNo ratings yet
- Certified List of Candidates For Congressional and Provincial Positions For The May 13, 2013 2013 National, Local and Armm ElectionsDocument2 pagesCertified List of Candidates For Congressional and Provincial Positions For The May 13, 2013 2013 National, Local and Armm ElectionsSunStar Philippine NewsNo ratings yet
- SAD Chapter 3Document44 pagesSAD Chapter 3Roman MarcosNo ratings yet
- Abolish The Electoral CollegeDocument4 pagesAbolish The Electoral CollegeMazerithNo ratings yet
- HR Business Partner SPHR in Dallas FT Worth TX Resume Patrick UszlerDocument2 pagesHR Business Partner SPHR in Dallas FT Worth TX Resume Patrick UszlerPatrickUszlerNo ratings yet
- Municipal Best Practices - Preventing Fraud, Bribery and Corruption FINALDocument14 pagesMunicipal Best Practices - Preventing Fraud, Bribery and Corruption FINALHamza MuhammadNo ratings yet
- AppendixDocument3 pagesAppendixAnnabel SeahNo ratings yet
- ADL 08 Corporate Governance V2Document21 pagesADL 08 Corporate Governance V2Razz Mishra100% (3)
- Certified List of Candidates For Congressional and Local Positions For The May 13, 2013 2013 National, Local and Armm ElectionsDocument2 pagesCertified List of Candidates For Congressional and Local Positions For The May 13, 2013 2013 National, Local and Armm ElectionsSunStar Philippine NewsNo ratings yet
- British Airways Work AssignmentDocument5 pagesBritish Airways Work Assignmentdoinitza_borshNo ratings yet
- Project Management - Lessons Learned TemplateDocument6 pagesProject Management - Lessons Learned TemplateYogeetaDeshmukh100% (1)
- (2009) MURRAY - Towards A Common Understanding of The Differences Between Purchasing, Procurement and Commissioning in The UK Public SectorDocument5 pages(2009) MURRAY - Towards A Common Understanding of The Differences Between Purchasing, Procurement and Commissioning in The UK Public SectorfranksmNo ratings yet
- Super Lab - FOIPDocument111 pagesSuper Lab - FOIPTeamWildroseNo ratings yet
- Midterm Module in SocSci2Document10 pagesMidterm Module in SocSci2Alvin Kris AlicNo ratings yet
- Senate Committee Finds 'No Evidence' of Voter Fraud in Michigan During 2020 ElectionDocument55 pagesSenate Committee Finds 'No Evidence' of Voter Fraud in Michigan During 2020 ElectionWXYZ-TV Channel 7 DetroitNo ratings yet
- HR Jobs:-Dear Candidates, Kindly Apply To The Below Given Email Address or Call To HR. 1.EDocument9 pagesHR Jobs:-Dear Candidates, Kindly Apply To The Below Given Email Address or Call To HR. 1.EPiya Madhukar MishraNo ratings yet
- Elections Data 3Document10 pagesElections Data 3Alex SammyNo ratings yet
- Federal Enterprise Architecture Framework v2 Highlights Key ComponentsDocument434 pagesFederal Enterprise Architecture Framework v2 Highlights Key ComponentsSDNo ratings yet
- Basics of MRP AreaDocument22 pagesBasics of MRP AreavarshadeepNo ratings yet
- TQM Management Checklist GuideDocument4 pagesTQM Management Checklist GuidessslucysssNo ratings yet
- BOARD of DIRECTORS Is A Body of Elected or Appointed Members Who Jointly Oversee The Activities of A Company or OrganizationDocument7 pagesBOARD of DIRECTORS Is A Body of Elected or Appointed Members Who Jointly Oversee The Activities of A Company or OrganizationAriel GamNo ratings yet
- The Andhra Pradesh Gazette: Published by AuthorityDocument2 pagesThe Andhra Pradesh Gazette: Published by AuthorityKittu KitsNo ratings yet
- Driving Innovation Through HRM - P&GDocument5 pagesDriving Innovation Through HRM - P&GVarun Pratap SinghNo ratings yet