Professional Documents
Culture Documents
DNS (Domain Name System) Tutorial at IETF-64: Ólafur Guðmundsson Peter Koch
Uploaded by
Atul BatraOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
DNS (Domain Name System) Tutorial at IETF-64: Ólafur Guðmundsson Peter Koch
Uploaded by
Atul BatraCopyright:
Available Formats
DNS (Domain Name System)
Tutorial @ IETF-64
DNS for Application Protocol Designers
Ólafur Guðmundsson
OGUD consulting
Peter Koch
DENIC eG
2005-11-06 DNS Tutorial @ IETF-64 1
ogud@ogud.com & pk@denic.de
Tutorial Overview
• Goal:
– Give the audience basic understanding of
DNS to be able to facilitate new uses of DNS
• Location of slides:
– http://stora.ogud.com/DNSTutorial.ppt
• Tutorial Focus: Big picture
- Not software help
- DNS != BIND
- No gory protocol details
2005-11-06 DNS Tutorial @ IETF-64 2
ogud@ogud.com & pk@denic.de
What is DNS?
• DNS is one of the core Internet Protocols
required for operation of the Internet
• Routing and DNS are the most important
infrastructure protocols as without them
nothing else will work
• DNS Provides:
– Mapping from names to addresses
– Mechanism to store and retrieve information
in a global data store
2005-11-06 DNS Tutorial @ IETF-64 3
ogud@ogud.com & pk@denic.de
DNS Data Model
DNS is global "loosely consistent" delegated database
• delegated -> contents are under local control
• loosely consistent -> shared information (within
constraints)
– does not need to match or be up-to date.
– operation is global with owners of "names" responsible for
serving up their own data.
• Data on wire is binary
• Domain names are case insensitive for [A-Z][a-z],
– case sensitive for others ( exämple.com != exÄmple.com)
• Hostname [A..Z0..9-] RFC952
– Restricts names that can be used
– IDN provides standard encoding for names in non-US_ASCII
2005-11-06 DNS Tutorial @ IETF-64 4
ogud@ogud.com & pk@denic.de
DNS tree
“.”
ORG COM DE IS UK XXX
IETF ogud ISOC DENIC
www EDU
2005-11-06 DNS Tutorial @ IETF-64 5
ogud@ogud.com & pk@denic.de
DNS Terms
• Domain name: any name represented in the DNS format
– foo.bar.example.
– \032br.example. (\032 == ASCII space binary value)
• DNS label: Presentation format
– each string between two "." (unless the dot is prefixed by “\”)
– i.e. foo.bar is 2 labels foo\.bar is 1 label
• DNS zone:
– a set of names that are under the same authority
– example.com and ftp.example.com, www.example.com
– Zone can be deeper than one label, like: .us, ENUM
• Delegation:
– Transfer of authority for a domain
• example.org is a delegation from org
• the terms parent and child will be used.
2005-11-06 DNS Tutorial @ IETF-64 6
ogud@ogud.com & pk@denic.de
More DNS terms
• RR: a single Resource Record
• RRSet: all RRs of same type at a name
– Minimum DNS transmission unit
– Sample RRSet:
Foo.example. 36000 IN TXT “Record #1”
Foo.Example. 36000 IN TXT “Record #2”
• TTL (Time To Live): The time an RRSet can be
cached/reused by a non- authoritative server
2005-11-06 DNS Tutorial @ IETF-64 7
ogud@ogud.com & pk@denic.de
DNS Elements
• Resolver
– stub: simple, only asks questions
– recursive: takes simple query and makes all
necessary steps to get the full answer,
• Server
– authoritative: the servers that contain the zone file for
a zone, one Primary, one or more Secondaries,
– caching: A recursive resolver that stores prior results
and reuses them
• Some perform both roles at the same time.
2005-11-06 DNS Tutorial @ IETF-64 8
ogud@ogud.com & pk@denic.de
DNS retrieval mode
• DNS is a "lookup service"
– Simple queries --> simple answers
• No search
• no 'best fit' answers
– Limited data expansion capability
• DNS reasons for success
– Simple
• "holy" Q-trinity: QNAME, QCLASS, QTYPE
– Clean
• Explicit transfer of authority
– Parent is authoritative for existence of delegation,
– Child is authoritative for contents.
2005-11-06 DNS Tutorial @ IETF-64 9
ogud@ogud.com & pk@denic.de
DNS Protocol on the wire
• Transport: 1 1 1 1 1 1
– UDP 512 bytes Payload, with 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5
+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
| ID |
TCP fallback +--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
|QR| Opcode |AA|TC|RD|RA| Z|AD|CD| RCODE |
+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
– EDNS0 (OPT RR) expands | QDCOUNT == 1 |
+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
UDP payload size by mutual | ANCOUNT |
+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
agreement.
| NSCOUNT |
+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
| ARCOUNT |
– TSIG hop by hop +--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+--+
Query section contains:
QNAME: <name in domain name format, variable length>
authentication and integrity QCLASS: 2 bytes
QTYPE: 2 bytes.
Red fields set by resolver in the query
• Retransmission: built in
– Resends timed out query to a
different server.
2005-11-06 DNS Tutorial @ IETF-64 10
ogud@ogud.com & pk@denic.de
DNS RR wire format
+------------------+-----+------+--------+----+-----------+
+ Domain name |type | class| TTL | RL | RDATA |
+------------------+-----+------+--------+----+-----------+
<variable> 2 2 4 2 <variable>
• Owner name (domain name)
– Encoded as sequence of labels
• Each label contains
– Length (1 byte)
– Name ([1..63] bytes)
– ogud.com 04ogud03com00
• Type : MX, A, AAAA, NS …
• CLASS: IN (other classes exist but not global)
• TTL: Time To Live in a cache
• RL: RD LENGTH: size of RDATA
• RDATA: The contents of the RR
– Binary blob, no TLV (Type Length Value).
2005-11-06 DNS Tutorial @ IETF-64 11
ogud@ogud.com & pk@denic.de
DNS Record Types:
• DNS Internal types
– Authority: NS, SOA,
• List names of Name Servers and Start Of Authority/zone.
– DNSSEC: DS, DNSKEY, RRSIG, NSEC
• Used for DNSSEC
– Meta types: OPT, TSIG, TKEY, SIG(0)
• Meta Types: Not stored in DNS zones, transfer information between DNS
nodes
– Indirect: CNAME, DNAME
• Indirect types, cause Resolver to change direction of search
– Server must have special processing code
• Terminal RR:
– Address records: A, AAAA,
– Informational: TXT, HINFO, KEY, SSHFP …
• carry information to applications
• Non Terminal RR: MX, SRV, PTR, KX, A6, NAPTR, AFSDB
• contain domain names that may lead to further queries.
2005-11-06 DNS Tutorial @ IETF-64 12
ogud@ogud.com & pk@denic.de
[jhc] Give example of
[jhc] Give example of
“longest match” – I
“longest match” – I
presume this is “most
presume this is “most
How DNS works
labels from most-
labels from most-
significant end”?
significant end”?
Got
Gotrid
ridofofDNS
DNSpackets
packets
are small to avoid
are small to avoid
arguments
argumentsand andwe
wesaid
said
that eariler
that eariler
Revist • DNS zone is loaded on authoritative servers,
RevistLongest
sentence.
Longestmatch
match
sentence.
– servers keep in sync using information in SOA RR
via AXFR, IXFR or other means.
• DNS caches only store data for a “short” time
– defined by TTL on RRSet.
• DNS Recursive Resolvers start at “longest
match” on query name they have when looking
for data, and follow delegations until an answer
or a negative answer is received.
– DNS transactions are fast if servers are reachable.
2005-11-06 DNS Tutorial @ IETF-64 13
ogud@ogud.com & pk@denic.de
DNS query
• QNAME: www.ietf.org
Root Server
• QCLASS: IN
• QTYPE: A. Ask org NS
Org Server
www.ietf.org
Ask ietf.org NS
Stub resolver
Recursive Ietf.org Server
www.ietf.org A Resolver
65.256.255.51 www.ietf.org A
65.256.255.51
2005-11-06 DNS Tutorial @ IETF-64 14
ogud@ogud.com & pk@denic.de
DNS Wildcards:
The area of most confusion:
FACTS
• Match ONLY non existing names
• Expansion is terminated by existing names
– Do not expand past zone boundaries
– Empty non-terminal name
• No RRSets present at this name
• But the name exists
2005-11-06 DNS Tutorial @ IETF-64 15
ogud@ogud.com & pk@denic.de
DNS wildcards: The area of most
confusion: MYTHS
• Record:
*.example MX 10 mail.example
– matches any name in zone example !!
– supplies RR type to names present that are
missing MX RRs
• Is added to MX RRSet at a name
– expands only one label
• www.*.example will expand
2005-11-06 DNS Tutorial @ IETF-64 16
ogud@ogud.com & pk@denic.de
Wildcard Match
• Contents of a zone:
*.example. TXT "this is a wildcard" example
www.example. A 192.0.2.1
jon.doe.example. A 192.0.2.5
• Name “doe.example”
exists w/o any RRtypes empty non-
terminal
• Name “jane.doe.example.”
will not be expanded from
wildcard
• Name: “jane.eod.example.” Matched.
2005-11-06 DNS Tutorial @ IETF-64 17
ogud@ogud.com & pk@denic.de
DNS rough corners
• UDP Packet size:
– 512 for standard DNS, 4K+ for EDNS0
• Keeping RRSets small is good practice.
• Lame delegations:
– Parent and children must stay in sync about name servers.
– Secondary servers must keep up-to date with Primary.
• problems areas: permissions, transfer protocol not getting through,
clock synchronization, old/renumbered primary/secondary, etc.
• Data integrity: Cache Poisoning
– DNS answer can be forged, in particular if query stream is visible
• use protected channel to recursive resolvers.
– TSIG, IPSEC, local host
• Broken/old DNS Software:
– Small percentage, but persistent base
2005-11-06 DNS Tutorial @ IETF-64 18
ogud@ogud.com & pk@denic.de
DNS Historic problems and
solutions: Static data
• DNS Update (RFC2136):
– adds the ability to change DNS contents of
the fly used a lot.
• Difficult to add/modify data due to operator
– DNS Secure Update (RFC3007) specifies
how to securely delegate capability to update
DNS names or name/type(s)
2005-11-06 DNS Tutorial @ IETF-64 19
ogud@ogud.com & pk@denic.de
DNS Historic problems and
solutions: Unknown RR types
• Early DNS implementation hard coded RR types.
– Unknown RR were/are dropped by some resolvers
– Unknown RR were not served by authoritative servers
• Implication: takes long time to introduce New RR types.
• Solution:
– RFC3597 defines that all DNS servers and resolvers MUST
• support unknown RR types and rules for defining them.
• suggests a common encoding in presentation format for them.
• Deployment:
– BIND-9, BIND-8.2.2, ANS, CNS, MS DNS-2003, DNSCache,
NSD, PowerDNS, Net::DNS, DNSJava, DNSPython.
2005-11-06 DNS Tutorial @ IETF-64 20
ogud@ogud.com & pk@denic.de
Current DNS Infrastructure
problems
• Old implementations still around as authoritative/caching servers
– Protocol has evolved over the last 20 years.
• Middle boxes have old/bad DNS software that is broken.
– Some Load balancers do stupid things,
– Firewalls apply yesterday’s DNS rules.
– Applications interfaces refuse to ask for unknown types
• Majority of the infrastructure
– is RFC3597 enabled.
– has EDNS0 support
• TCP DNS queries are frequently blocked.
• "Are you affected" Simple test:
– http://stora.ogud.com/DNSSEC/unknown/index.html
• Right now shell scripts, soon a java applet.
2005-11-06 DNS Tutorial @ IETF-64 21
ogud@ogud.com & pk@denic.de
DNS Operational problems
• Low TTL: if TTL is low, RRSet is cached for
short time and frequent lookups are required:
– negative effects: DoS on self and infrastructure,
slower connections
– positive effects: Highly dynamic and allows primitive
load balancing
• Bad delegations:
– NS out of date in parent
– NS contains random data to overcome registry
requirements
• Old Software still in use after vendor
recommends retirement
2005-11-06 DNS Tutorial @ IETF-64 22
ogud@ogud.com & pk@denic.de
DNS Operational Excuses
• Opposition to placing data in DNS is
sometimes based on “arguments” like:
• Not supported by our software
– Provisioning, Authorative servers, resolvers, firewalls,
middleboxes,
» take your pick.
• Do not feel like it
– Turf war, politics ….
– …..
2005-11-06 DNS Tutorial @ IETF-64 23
ogud@ogud.com & pk@denic.de
DNS API issues
• Whole or none of RRSet will arrive,
– in non determined order.
• DNS Resolver API should
– Return known weighed DNS RRSet in weighed order
– other RRSets in “random” order.
• DNS data should reside in one place and one place only
– at name, or at <prefix>.name
– zone wide defaults
• there are no zone wide defaults, since the "zone" is an artificial boundary for
management purpose
– Some applications have said that if RR does not exist at name then look
for zone default at apex,
• Zone cut is hard to find by stub resolvers,
• hierarchy in naming does not necessarily imply hierarchy in network
administration.
• Data at apex are also bad due to "apex overload“
– Tree climbing == BAD
2005-11-06 DNS Tutorial @ IETF-64 24
ogud@ogud.com & pk@denic.de
DNS API qualities and Good
Tools
• API should
– Be simple and expandable,
– Return good/appropriate error codes
– Allow server selection and query for any type.
– Seamlessly provide ENDS and TSIG
• Good Stub Resolver tool kits:
– Perl: Net::DNS and Net::DNS::SEC,
– Java: DNSJava,
– Python: dnspython
– C: not aware of any
– C++: we do not know
2005-11-06 DNS Tutorial @ IETF-64 25
ogud@ogud.com & pk@denic.de
DNS Sub Typing ISSUE
• Some RR types are "containers", e.g.
– KEY (the original)
– NAPTR
– TXT (with the RFC1464 convention)
• DNS responses MUST consist of complete RRSets
– You cannot query for partial matches (only holy Q-Trinity: QNAME,
QTYPE, QCLASS)
• Resolver cannot ask for a subset of an RRSet, e.g.
– at most eight address records (A RRs) for a given name or
– only those MX RRs with priority of less than 100
– all TXT RRs containing "money".
• Applications (or specialized API) will have to select their RRs from
the response, potentially dumping larger parts of the RRSet,
depending on one or more secondary qualifiers buried within
RDATA
2005-11-06 DNS Tutorial @ IETF-64 26
ogud@ogud.com & pk@denic.de
SubTyping side effects
• Subtyping results in larger responses
– Multitude of different ENUM services using NAPTR
• Subtyping can be avoided by
– dedicated types instead of type/subtype
– selector prefixes (see SRV)
• Method of choice depends on number and
nature of subtypes expected and the necessity
to deal with wildcards
2005-11-06 DNS Tutorial @ IETF-64 27
ogud@ogud.com & pk@denic.de
DNSSEC: Data integrity and
authentication for DNS
• Full Name: DNS Security Extensions
– RFCs 4033, 4034, 4035
• Role: Protect DNS and the data it carries
– How done: view from 10 km.
• DNS RRSet is signed by the zone it belongs to.
• zone DS RRSet is vouched for by parent zone.
• What DNSSEC does not do:
– Make data in DNS any more correct.
2005-11-06 DNS Tutorial @ IETF-64 28
ogud@ogud.com & pk@denic.de
DNSSEC: More details
• Data protections
– Each DNS RRSet has a special RRSIG containing a
signature by the zone private key, for a certain time
period
• Existence proof:
– Chain of NSEC records lists all names in a zone and
their RR types. (authentic proof/denial of existence)
• Parent signs a fingerprint of child's Key Signing
DNSKEY (DS RR)
– allows transition from a secure parent zone to a
secure child zone.
2005-11-06 DNS Tutorial @ IETF-64 29
ogud@ogud.com & pk@denic.de
DNSSEC: impacts
• Zones
– become larger
– need periodic maintenance
– have to deal with key management
• Resolvers need to know Secure Entry Points to
signed sub trees.
– Changes over time, needs updating.
• Implementations supporting DNSSEC:
– BIND-9, DNSJava, Net::DNS::SEC, NSD, ANS, CNS
2005-11-06 DNS Tutorial @ IETF-64 30
ogud@ogud.com & pk@denic.de
What does DNSSEC provide to
applications?
1. DNS answer with verifiably signed RRSet(s) is
known to be identical to what zone published.
2. Widely deployed DNSSEC allows application to
place more important data in DNS
• unsigned keying info
• IPSECKEY, SSHFP
• spoof proof service location
• other...
2005-11-06 DNS Tutorial @ IETF-64 31
ogud@ogud.com & pk@denic.de
SRV (SeRVice) Record
• Provides a mechanism to place a service on named
host(s) at specified port.
• Used extensively in MS Active Directory
– Also used by some IM application like Jabber.
• recurring task: given (new) service named COOL, need
to offer it
– old solution: aliases "ftp", "www", ...
– problem: needs well known port, no exceptions;
• single target (server) or approximately evenly distributed across
multiple addresses
2005-11-06 DNS Tutorial @ IETF-64 32
ogud@ogud.com & pk@denic.de
Generalize MX: that COOL SRV
• COOL service in example.org
_cool._tcp.example.org SRV 0 0 5133 srv55.mega.example
_cool._tcp.example.org SRV 10 20 9876 srv33.mega.example.
_cool._tcp.example.org SRV 10 20 3456 srv44.mega.example.
_cool._tcp.example.org SRV 10 40 6738 srv66.mega.example.
“_” avoids conflicts with hostnames
• Services need to be registered
– currently under discussion: separate registry
– this is not too good for local service location (-> tree climbing)
20
0 20
40
2005-11-06 DNS Tutorial @ IETF-64 33
ogud@ogud.com & pk@denic.de
When to use SRV
• SRV works best if you have a TCP or UDP
service and want to be able to delegate
and distribute
• SRV is widely deployed and supported
• See RFC 2782
2005-11-06 DNS Tutorial @ IETF-64 34
ogud@ogud.com & pk@denic.de
NAPTR
• Other common task: Map name to URL
• SRV doesn‘t help
– No local part
– No variable scheme
• Naming Authority Pointer: NAPTR
– order 16 bit value
– preference 16 bit value
– flags character-string
– service character-string
– regexp character-string
– replacement domain-name
2005-11-06 DNS Tutorial @ IETF-64 35
ogud@ogud.com & pk@denic.de
NAPTR and beyond: DDDS
• NAPTR is embedded in a complete
framework
• DDDS == Dynamic Delegation Discovery
System
• Used in ENUM and ONS (the RFID name
space)
– These create their own name spaces
2005-11-06 DNS Tutorial @ IETF-64 36
ogud@ogud.com & pk@denic.de
S-NAPTR
• SRV and NAPTR combined (RFC 3958)
• Avoids application specific DDDS
overhead
• NAPTR leads to more NAPTR or SRV
• SRVs lead to A (or AAAA)
2005-11-06 DNS Tutorial @ IETF-64 37
ogud@ogud.com & pk@denic.de
Design Choices for placing new
information in DNS.
• New class
– You need to supply the root servers for it
• New Suffix
– Talk to ICANN
• Reuse TXT (or some other type)
• <prefix>.name
• New Type
2005-11-06 DNS Tutorial @ IETF-64 38
ogud@ogud.com & pk@denic.de
Placing New information in DNS:
Reuse existing Type
• TXT may appear as the obvious choice
– No semantics
– RFC 1464 subtyping
– prefixing could help, but has its own problems
– TXT wastes space, this is still important
– If new RRSet is large you want EDNS0 support
• Modern software does this and unknown types as
well!!!!
– MORAL: Fight for local upgrades, do not force the whole
Internet to work around your local issues.
2005-11-06 DNS Tutorial @ IETF-64 39
ogud@ogud.com & pk@denic.de
Placing New information in DNS:
Name prefix, magic name
• Selector put in front of (underneath) domain
name:
– _axfr.example.org APL 1:192.0.2.3
– May interfere with zone maintainer’s naming policy
– Prefix may end up in a different zone
– Wildcards will not work like expected, i.e.
_prefix.*.example.org does not expand
– No registry for prefixes
• Magic name, e.g. www
– Overloading of multiple names in single application
server
– May conflict with naming policy
2005-11-06 DNS Tutorial @ IETF-64 40
ogud@ogud.com & pk@denic.de
New RR Type Benefits
• Full control over contents
• Application centered semantics
• Simpler for applications to parse
– If your specification is simple: KISS
• No collisions, smaller answers
2005-11-06 DNS Tutorial @ IETF-64 41
ogud@ogud.com & pk@denic.de
New RR Type Phase-in
• When you design the new RR type to be
used with the existing namespace
• What does the absence of the type at a name
mean?
• Specify:
– Feature not available
– Feature not supported
– Use application default
• Do not overdo the problem!
2005-11-06 DNS Tutorial @ IETF-64 42
ogud@ogud.com & pk@denic.de
How to get a new DNS RR type
• Technical Rules (see RFC 3597)
1. No additional section processing
2. No name compression of embedded domain names
3. Clean definition, no overly complicated structure
• Process: (being simplified RFC2929bis)
1. Write an ID, get review by people that understand your protocol,
update draft.
2. Ask DNS experts (DNS WG chairs) for quick review, update ID
3. Ask DNS WG(s) for review
4. Submit to IESG, you get type code from IANA after IESG
processes
5. Advertise new type code
2005-11-06 DNS Tutorial @ IETF-64 43
ogud@ogud.com & pk@denic.de
How to enable the use of a new
type?
• Make sure your
– software is “modern"
– middle-ware boxes do not get in the way,
• Fight for site updates.
• Provide tools to
– convert new RR type from textual format to RFC3597
portable format for zone inclusion,
– Use dynamic update to provision new type RRSets
• Good tools: Perl NET::DNS, DNSJava,
• Modern Servers:
– BIND-9, MS DNSServer2003, NSD, PowerDNS, ANS,
CNS
2005-11-06 DNS Tutorial @ IETF-64 44
ogud@ogud.com & pk@denic.de
Optimization considered evil
• Problem:
– Frequently Non-terminal records proposed demand that terminal
records be returned in answer ==> Additional section processing
• Facts:
1. Additional section processing is done in servers
2. Before updated servers are deployed RR type aware resolvers need to
do all work.
3. Not all authoritative servers may have the necessary additional records
4. Additional records may not fit
5. Recursive resolver may have data already
6. Roundtrips are cheap,
7. Lasy resolver writer will ASSUME additional section processing is done
• Result:
– Recursive Resolver has to be able to do work forever,
• Moral: Do not attempt to optimize DNS, it causes problems.
2005-11-06 DNS Tutorial @ IETF-64 45
ogud@ogud.com & pk@denic.de
RFC starting reading list
• DNS related RFC 100+
– Many obsoleted
• Important ones
– 1034, 1035 Original specification
– 4033, 4034, 4035 DNSSEC
– 1123, 2181 Clarifications
– 3597, 2136, 1996, 1995, 3007 Major protocol
enhancements
– 3833 Threat Analysis for DNS
2005-11-06 DNS Tutorial @ IETF-64 46
ogud@ogud.com & pk@denic.de
Pointers to more information
• IETF working groups
– DNS EXTensions: http://www.dnsext.org
– DNS Operations: http://www.dnsop.org
• Individual sites
– http://www.dns.net/dnsrd
– http://www.dnssec.net
2005-11-06 DNS Tutorial @ IETF-64 47
ogud@ogud.com & pk@denic.de
More resources
• DNS book list
– http://www.networkingbooks.org/dns
• DNS Software tools:
– BIND9: http://www.isc.org
– DNSJava: http://www.dnsjava.org
– Perl: http://www.net-dns.org
– Nominum: ANS, CNS http://www.nominum.com
– Python: http://www.dnspython.org
- NSD http://www.nlnetlabs.nl/nsd/
2005-11-06 DNS Tutorial @ IETF-64 48
ogud@ogud.com & pk@denic.de
You might also like
- Update Your DNS Server for Improved Internet StabilityDocument42 pagesUpdate Your DNS Server for Improved Internet StabilityReza AdityaNo ratings yet
- dns1 PresentationDocument30 pagesdns1 Presentationnooby90No ratings yet
- DNSDocument70 pagesDNSSaiVamsiKrrishnaNo ratings yet
- DNS & Nat & VPNDocument52 pagesDNS & Nat & VPNDevendra BhavsarNo ratings yet
- Material de DNS e BindDocument27 pagesMaterial de DNS e Bindrobertofca2266No ratings yet
- eDNS01 DNSConceptsDocument22 pageseDNS01 DNSConceptsShyam KhadkaNo ratings yet
- Black Ops of DNS Chaos Communications Camp 2003: Dan Kaminsky, CISSP Senior Security ConsultantDocument41 pagesBlack Ops of DNS Chaos Communications Camp 2003: Dan Kaminsky, CISSP Senior Security Consultantapi-16329593No ratings yet
- DNS Session 1: FundamentalsDocument113 pagesDNS Session 1: FundamentalsTony KinyuaNo ratings yet
- Screenshot 2023-04-08 at 7.03.30 AMDocument23 pagesScreenshot 2023-04-08 at 7.03.30 AMJaabir MacalinyareNo ratings yet
- ProtocolDocument31 pagesProtocolwahidNo ratings yet
- SARA IT DNS PresentationDocument33 pagesSARA IT DNS PresentationIyad AliNo ratings yet
- Translating Addresses: Computer NetworksDocument50 pagesTranslating Addresses: Computer NetworksfalthoomanNo ratings yet
- 15-441 Lecture on DNS Design and OperationDocument37 pages15-441 Lecture on DNS Design and OperationJay ShrotriyaNo ratings yet
- Tshooting DNS and Exchange 2000Document78 pagesTshooting DNS and Exchange 2000RamRyanNo ratings yet
- DNS - Domain Name System: TCP/IP ClassDocument60 pagesDNS - Domain Name System: TCP/IP ClasssrihariNo ratings yet
- FunWithLDAPandKerberos Flathers Troopers2019 PDFDocument101 pagesFunWithLDAPandKerberos Flathers Troopers2019 PDFdaniel restrepoNo ratings yet
- Lesson04 - Config and Manage DNS Server RoleDocument64 pagesLesson04 - Config and Manage DNS Server RoleKendell Blaze Jno-CharlesNo ratings yet
- Manual-IP DNS PDFDocument5 pagesManual-IP DNS PDFNaz LunNo ratings yet
- Implement DNS and DHCP for Network AdministrationDocument93 pagesImplement DNS and DHCP for Network AdministrationNgộ Nguyễn ĐạiNo ratings yet
- Structured Naming: Internet Naming Service: DNSDocument70 pagesStructured Naming: Internet Naming Service: DNSNeenu PrasannanNo ratings yet
- Oracle Net Services: Performance, Scalability, HA and Security Best PracticesDocument56 pagesOracle Net Services: Performance, Scalability, HA and Security Best PracticesKannan SaravananNo ratings yet
- DNS Security: CH 2: DNS Overview: Protocol, Architecture, and Applications Updated 2-10-15Document42 pagesDNS Security: CH 2: DNS Overview: Protocol, Architecture, and Applications Updated 2-10-15Eric ChanNo ratings yet
- Presentation of Domain Name SystemDocument33 pagesPresentation of Domain Name SystemPiyushank GuptaNo ratings yet
- DNS/DNSSEC WorkshopDocument39 pagesDNS/DNSSEC WorkshopMohamad ShidiqNo ratings yet
- DNS Domain Name Service GuideDocument70 pagesDNS Domain Name Service GuideAndry Imam MustofaNo ratings yet
- 20741B - 04-Implementing DNSDocument68 pages20741B - 04-Implementing DNSSanitaracNo ratings yet
- Active Directory Domain ServicesDocument10 pagesActive Directory Domain ServicesthissiteisfailNo ratings yet
- Chapter 17Document22 pagesChapter 17Kushagra TiwaryNo ratings yet
- DNSDocument8 pagesDNSKarthik KeyanNo ratings yet
- DNS, DHCP, SNMP & Network SecurityDocument22 pagesDNS, DHCP, SNMP & Network SecurityArun PatelNo ratings yet
- Structured Naming: Internet Naming Service: DNSDocument63 pagesStructured Naming: Internet Naming Service: DNSMehari TemesgenNo ratings yet
- 08 Ipv6 Dns PDFDocument14 pages08 Ipv6 Dns PDFElquia MadridNo ratings yet
- 15-744: Computer Networking: L-20 Data-Oriented NetworkingDocument45 pages15-744: Computer Networking: L-20 Data-Oriented NetworkingtakenoveraccountNo ratings yet
- Presentation - Oracle Net ServicesDocument56 pagesPresentation - Oracle Net ServicesTruong HoangNo ratings yet
- Manual - IP - DNS - MikroTik WikiDocument5 pagesManual - IP - DNS - MikroTik Wikimona_mi8202No ratings yet
- DNS Packet StructureDocument8 pagesDNS Packet StructureSchool AppNo ratings yet
- Distributed Systems: Domain Name SystemDocument26 pagesDistributed Systems: Domain Name SystemArjuna KrishNo ratings yet
- DNS TranslationDocument22 pagesDNS TranslationZ GooNo ratings yet
- Dnssec 20122014Document85 pagesDnssec 20122014Muhammad Amal Al-Ghifari0% (1)
- 15-441 Computer NetworkingDocument37 pages15-441 Computer NetworkingShaveta KhepraNo ratings yet
- Basic ConceptsDocument84 pagesBasic Conceptstuan anhNo ratings yet
- DNS InfoDocument79 pagesDNS InfoKevin_RayNo ratings yet
- DNS, DHCP, SNMP & Network SecurityDocument22 pagesDNS, DHCP, SNMP & Network SecurityNabendu GhoshNo ratings yet
- Network Documentation and NetdotDocument37 pagesNetwork Documentation and NetdotislamNo ratings yet
- Advanced Computer Networks - CS716 Power Point Slides Lecture 42Document48 pagesAdvanced Computer Networks - CS716 Power Point Slides Lecture 42Taran AulakhNo ratings yet
- DNS Zone File ExplainedDocument109 pagesDNS Zone File Explainedmicham1209No ratings yet
- Dns 100Document12 pagesDns 100AbhiNo ratings yet
- AL Protocol DNSDocument25 pagesAL Protocol DNSVivek BhattNo ratings yet
- Application LayerDocument33 pagesApplication Layerramna kNo ratings yet
- Attacking Distributed Systems The DNS Case Study: Dan Kaminsky, CISSP Senior Security ConsultantDocument36 pagesAttacking Distributed Systems The DNS Case Study: Dan Kaminsky, CISSP Senior Security Consultantd.s.gustedNo ratings yet
- Web AdminDocument3 pagesWeb AdmingazalmalhotraNo ratings yet
- Lecture 9: Ip Variations: Ipv6, Multicast, AnycastDocument42 pagesLecture 9: Ip Variations: Ipv6, Multicast, AnycastSharifu KifikaNo ratings yet
- Understand DNS in 40 charactersDocument38 pagesUnderstand DNS in 40 charactersAmed HamdaniNo ratings yet
- DNS RecordsDocument4 pagesDNS RecordsvineethNo ratings yet
- Week3 2Document18 pagesWeek3 2Ambreen AsifNo ratings yet
- Evaluation of Some SMTP Testing, SSL Checkers, Email Delivery, Email Forwarding and WP Email Tools: Evaluation of Some SMTP Testing, SSL Checkers, Email Delivery, Email Forwarding and WordPress Email ToolsFrom EverandEvaluation of Some SMTP Testing, SSL Checkers, Email Delivery, Email Forwarding and WP Email Tools: Evaluation of Some SMTP Testing, SSL Checkers, Email Delivery, Email Forwarding and WordPress Email ToolsNo ratings yet
- Evaluation of Some SMTP Testing, Email Verification, Header Analysis, SSL Checkers, Email Delivery, Email Forwarding and WordPress Email ToolsFrom EverandEvaluation of Some SMTP Testing, Email Verification, Header Analysis, SSL Checkers, Email Delivery, Email Forwarding and WordPress Email ToolsNo ratings yet
- Basic Linux Terminal Tips and Tricks: Learn to Work Quickly on the Command LineFrom EverandBasic Linux Terminal Tips and Tricks: Learn to Work Quickly on the Command LineNo ratings yet
- IBM Traveler Steps 8.5Document39 pagesIBM Traveler Steps 8.5Inadidas86No ratings yet
- Resume IT ManagerDocument3 pagesResume IT ManagerImran Ali ShahNo ratings yet
- Mail RoutingDocument30 pagesMail RoutingAlvin LeeNo ratings yet
- PMP MaterialDocument330 pagesPMP MaterialjogenderNo ratings yet
- Quiz 5 - CS690 A1 Network ..Document7 pagesQuiz 5 - CS690 A1 Network ..Nishant KawaNo ratings yet
- Take Assessment - EWAN Chapter 3 - CCNA Exploration: Accessing The WAN (Version 4.0)Document11 pagesTake Assessment - EWAN Chapter 3 - CCNA Exploration: Accessing The WAN (Version 4.0)pkperNo ratings yet
- Syllabus in Comp. Science 4 (Network Technology) : Philippine Science High SchoolDocument7 pagesSyllabus in Comp. Science 4 (Network Technology) : Philippine Science High SchoolAlexander Bermejo AvilaNo ratings yet
- CCIE Routing and Switching Exam Quick Reference Sheets by Anthony Sequeira - ch1Document4 pagesCCIE Routing and Switching Exam Quick Reference Sheets by Anthony Sequeira - ch1Saqib MullaNo ratings yet
- FortiSwitch Workshop v1.5.3 Handouts Lab PDFDocument153 pagesFortiSwitch Workshop v1.5.3 Handouts Lab PDFKossi DOHNo ratings yet
- SN2700 Open Ethernet Switch: HighlightsDocument3 pagesSN2700 Open Ethernet Switch: HighlightsKhawar NehalNo ratings yet
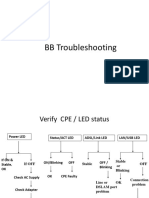
- BB Troubleshooting For E4-E5 FinalDocument21 pagesBB Troubleshooting For E4-E5 FinalManoj BorahNo ratings yet
- Computer Networks - A Top Down Approach: Notes (Chapters 1, 2, 3, 9)Document69 pagesComputer Networks - A Top Down Approach: Notes (Chapters 1, 2, 3, 9)Joe MamaNo ratings yet
- FRAGMENTATIONDocument13 pagesFRAGMENTATIONVinayKumarSingh100% (1)
- 310-302 Latest Test KingDocument96 pages310-302 Latest Test KingFarrukh HanifNo ratings yet
- Customer Presentation AZFW and AZFM NDADocument27 pagesCustomer Presentation AZFW and AZFM NDAtarunsood2009No ratings yet
- 479-0244-Anybus Communicator CAN PROFINET-IO User ManualDocument89 pages479-0244-Anybus Communicator CAN PROFINET-IO User ManualvarunshyamNo ratings yet
- Web Security Considerations:: Chapter 16 - Transport-Level SecurityDocument12 pagesWeb Security Considerations:: Chapter 16 - Transport-Level SecurityRutuja PatilNo ratings yet
- OcNOS-SP MPLS Config GuideDocument1,812 pagesOcNOS-SP MPLS Config GuideNicu MusteataNo ratings yet
- HomePlug AV Network Architecture OverviewDocument6 pagesHomePlug AV Network Architecture OverviewsanthoshNo ratings yet
- Determining Whether An Avamar System Is Experiencing A Time Synchronization (NTP) Issue. - Dell USDocument4 pagesDetermining Whether An Avamar System Is Experiencing A Time Synchronization (NTP) Issue. - Dell USDaniel KhantivongNo ratings yet
- Synology DiskStation MIB GuideDocument29 pagesSynology DiskStation MIB GuideJasper WongNo ratings yet
- Lab1: Learning About Switches: 1 ObjectivesDocument4 pagesLab1: Learning About Switches: 1 ObjectivesPrinoNo ratings yet
- Mobile Computing Unit 5Document138 pagesMobile Computing Unit 5prak530No ratings yet
- Active Directory Migration Tool Steps GuideDocument14 pagesActive Directory Migration Tool Steps GuidejammiziNo ratings yet
- Optimize Modbus Master SettingsDocument16 pagesOptimize Modbus Master SettingsJimmy F HernandezNo ratings yet
- 123 - Ceragon - IP-10G Licensing - Presentation v1.4Document29 pages123 - Ceragon - IP-10G Licensing - Presentation v1.4mehdi_mehdiNo ratings yet
- Run CLI commands in Asterisk shell scriptDocument5 pagesRun CLI commands in Asterisk shell scriptmr.himNo ratings yet
- BRKMPL-1101 - 2012 - San Diego PDFDocument90 pagesBRKMPL-1101 - 2012 - San Diego PDFAnonymous cRxoHJ32QvNo ratings yet
- Barracuda F Series FirewallDocument6 pagesBarracuda F Series FirewallVenugopal Athiur Ramachandran0% (1)
- 7000HS MHS Security Gateway DatasheetDocument4 pages7000HS MHS Security Gateway DatasheetDubem JavapiNo ratings yet
- Arp Spoofing Windows PDFDocument0 pagesArp Spoofing Windows PDFalsamixersNo ratings yet
- Data SheetDocument16 pagesData SheetGisele RomaniNo ratings yet
- CSSE280: Introduction to Web Programming</titleDocument30 pagesCSSE280: Introduction to Web Programming</titleGamal BohoutaNo ratings yet